1、批量调用POC扫描
当出现一个新的漏洞时,一般情况下公开的POC都是扫描单个目标,但是测试的时候基本都是几个网段,当然也有框架可以调用POC批量扫描,但是有时候某工具不能批量扫描时,需要自己去写个调用工具命令的脚本,因为不可能去修改工具满足框架的调用吧。下边是我用os模块编写的两个案例。
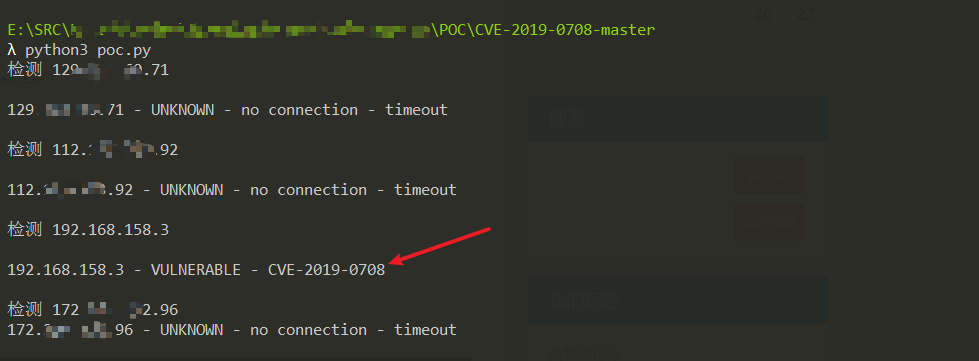
2、POC批量扫描
#!/usr/bin/python3
#-*- coding:utf-8 -*-
import os
import sys
def main():
path=r"E:xxxPOCCVE-2019-0708-master
dpscan.exe "
filename="ip.txt"
with open(filename,'r') as file:
for line in file:
try:
result = os.popen(path + line).read()
print("检测 "+line)
print(result)
except Exception as e:
print("Path error")
print(e)
if __name__ == '__main__':
main()
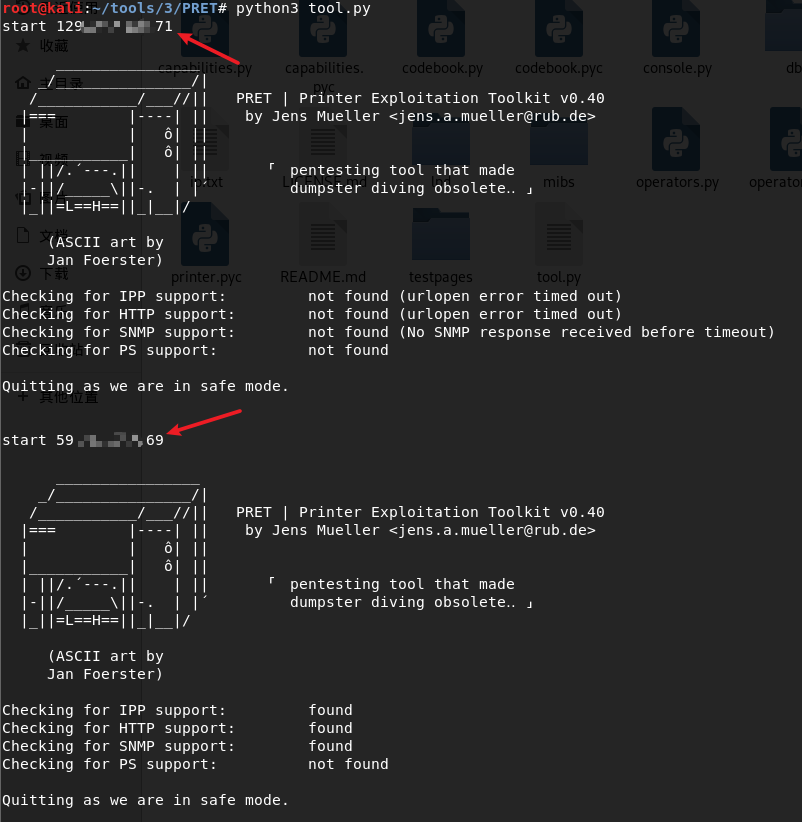
3、工具批量扫描,以PRET为例
#!/usr/bin/python3
#-*- coding:utf-8 -*-
import os
import sys
path="python pret.py -s "
file=open('ip.txt','r')
for line in file:
x=line.strip()
result=os.popen(path+x+' ps').read()
print("start"+line)
print(result)
如下图是遍历扫描的结果
文章参考:
os大全
https://www.runoob.com/python/os-file-methods.html