测试文件:https://adworld.xctf.org.cn/media/task/attachments/a5c0e8322d9645468befabddfe0cb51d.exe
1.准备
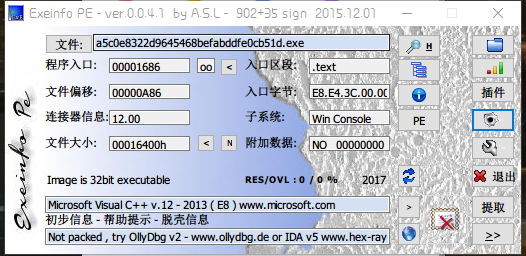
获取信息
- 32位文件
2.IDA打开
1 int __cdecl main(int argc, const char **argv, const char **envp) 2 { 3 unsigned int v3; // edx 4 unsigned int v4; // ecx 5 __m128i v5; // xmm1 6 unsigned int v6; // esi 7 const __m128i *v7; // eax 8 __m128i v8; // xmm0 9 int v9; // eax 10 char v11; // [esp+0h] [ebp-CCh] 11 char v12; // [esp+1h] [ebp-CBh] 12 char v13; // [esp+64h] [ebp-68h] 13 char v14; // [esp+65h] [ebp-67h] 14 unsigned int v15; // [esp+C8h] [ebp-4h] 15 16 printf("please input your flah:"); 17 v11 = 0; 18 memset(&v12, 0, 0x63u); 19 scanf("%s", &v11); 20 v13 = 0; 21 memset(&v14, 0, 0x63u); 22 sub_401000(&v15, &v13, (unsigned __int8 *)&v11, strlen(&v11)); 23 v3 = v15; 24 v4 = 0; 25 if ( v15 ) 26 { 27 if ( v15 >= 0x10 ) 28 { 29 v5 = _mm_load_si128((const __m128i *)&xmmword_414F20);// 这部分对我们的结果没有影响 30 v6 = v15 - (v15 & 0xF); 31 v7 = (const __m128i *)&v13; 32 do 33 { 34 v8 = _mm_loadu_si128(v7); 35 v4 += 16; 36 ++v7; 37 _mm_storeu_si128((__m128i *)&v7[-1], _mm_xor_si128(v8, v5)); 38 } 39 while ( v4 < v6 ); 40 } 41 for ( ; v4 < v3; ++v4 ) // 对每位字符进行异或0x25 42 *(&v13 + v4) ^= 0x25u; 43 } 44 v9 = strcmp(&v13, "you_know_how_to_remove_junk_code");// 处理之后的字符串为"you_know_how_to_remove_junk_code" 45 if ( v9 ) 46 v9 = -(v9 < 0) | 1; 47 if ( v9 ) 48 printf("wrong "); 49 else 50 printf("correct "); 51 system("pause"); 52 return 0; 53 }
其中的一些函数解释
__m128i _mm_load_si128 (__m128i *p); //返回可以存放在代表寄存器的变量中的值,即*p的值 __m128i _mm_load_si128 (__m128i *p); //返回可以存放在代表寄存器的变量中的值,即*p的值 void _mm_storeu_si128 ( __m128i *p, __m128i a); //将__m128i 变量a的值存储到p所指定的变量中去;
3.代码分析
这道题思路很清晰,就是逆向操作结果字符串就行。
我们输入v11,在下面有个关键的sub_401000(&v15, &v13, (unsigned __int8 *)&v11, strlen(&v11));函数

1 signed int __usercall sub_401000@<eax>(unsigned int *a1@<edx>, _BYTE *a2@<ecx>, unsigned __int8 *a3, unsigned int a4) 2 { 3 int v4; // ebx 4 unsigned int v5; // eax 5 int v6; // ecx 6 unsigned __int8 *v7; // edi 7 int v8; // edx 8 bool v9; // zf 9 unsigned __int8 v10; // cl 10 char v11; // cl 11 _BYTE *v12; // esi 12 unsigned int v13; // ecx 13 int v14; // ebx 14 unsigned __int8 v15; // cl 15 char v16; // dl 16 _BYTE *v18; // [esp+Ch] [ebp-Ch] 17 unsigned int *v19; // [esp+10h] [ebp-8h] 18 int v20; // [esp+14h] [ebp-4h] 19 unsigned int v21; // [esp+14h] [ebp-4h] 20 int i; // [esp+24h] [ebp+Ch] 21 22 v4 = 0; 23 v18 = a2; 24 v5 = 0; 25 v6 = 0; 26 v19 = a1; 27 v20 = 0; 28 if ( !a4 ) 29 return 0; 30 v7 = a3; 31 do 32 { 33 v8 = 0; 34 v9 = v5 == a4; 35 if ( v5 < a4 ) 36 { 37 do 38 { 39 if ( a3[v5] != 32 ) 40 break; 41 ++v5; 42 ++v8; 43 } 44 while ( v5 < a4 ); 45 v9 = v5 == a4; 46 } 47 if ( v9 ) 48 break; 49 if ( a4 - v5 >= 2 && a3[v5] == 13 && a3[v5 + 1] == 10 || (v10 = a3[v5], v10 == 10) ) 50 { 51 v6 = v20; 52 } 53 else 54 { 55 if ( v8 ) 56 return 4294967252; 57 if ( v10 == 61 && (unsigned int)++v4 > 2 ) 58 return 4294967252; 59 if ( v10 > 0x7Fu ) 60 return 4294967252; 61 v11 = byte_414E40[v10]; 62 if ( v11 == 127 || (unsigned __int8)v11 < 0x40u && v4 ) 63 return 4294967252; 64 v6 = v20++ + 1; 65 } 66 ++v5; 67 } 68 while ( v5 < a4 ); 69 if ( !v6 ) 70 return 0; 71 v12 = v18; 72 v13 = ((unsigned int)(6 * v6 + 7) >> 3) - v4; 73 if ( v18 && *v19 >= v13 ) 74 { 75 v21 = 3; 76 v14 = 0; 77 for ( i = 0; v5; --v5 ) 78 { 79 v15 = *v7; 80 if ( *v7 != 13 && v15 != 10 && v15 != 32 ) 81 { 82 v16 = byte_414E40[v15]; 83 v21 -= v16 == 64; 84 v14 = v16 & 0x3F | (v14 << 6); 85 if ( ++i == 4 ) 86 { 87 i = 0; 88 if ( v21 ) 89 *v12++ = BYTE2(v14); 90 if ( v21 > 1 ) 91 *v12++ = BYTE1(v14); 92 if ( v21 > 2 ) 93 *v12++ = v14; 94 } 95 } 96 ++v7; 97 } 98 *v19 = v12 - v18; 99 return 0; 100 } 101 *v19 = v13; 102 return -42; 103 }
对于这段函数实际上是base64解密,关键代码在于
if ( v18 && *v19 >= v13 ) { v21 = 3; v14 = 0; for ( i = 0; v5; --v5 ) { v15 = *v7; if ( *v7 != 13 && v15 != 10 && v15 != 32 ) { v16 = byte_414E40[v15]; v21 -= v16 == 64; v14 = v16 & 0x3F | (v14 << 6); if ( ++i == 4 ) // 4字节为一组处理 { i = 0; if ( v21 ) // 分为3字节输出 *v12++ = BYTE2(v14); if ( v21 > 1 ) *v12++ = BYTE1(v14); if ( v21 > 2 ) *v12++ = v14; } } ++v7; }
要了解base64加密原理可以看:https://www.cnblogs.com/Mayfly-nymph/p/11644823.html
解密代码可以看:https://blog.csdn.net/prsniper/article/details/7097643
byte_414E40为
00414E40 7F 7F 7F 7F 7F 7F 7F 7F 7F 7F 7F 7F 7F 7F 7F 7F ................ 00414E50 7F 7F 7F 7F 7F 7F 7F 7F 7F 7F 7F 7F 7F 7F 7F 7F ................ 00414E60 7F 7F 7F 7F 7F 7F 7F 7F 7F 7F 7F 3E 7F 7F 7F 3F ...........>...? 00414E70 34 35 36 37 38 39 3A 3B 3C 3D 7F 7F 7F 40 7F 7F 456789:;<=...@.. 00414E80 7F 00 01 02 03 04 05 06 07 08 09 0A 0B 0C 0D 0E ................ 00414E90 0F 10 11 12 13 14 15 16 17 18 19 7F 7F 7F 7F 7F ................ 00414EA0 7F 1A 1B 1C 1D 1E 1F 20 21 22 23 24 25 26 27 28 ....... !"#$%&'( 00414EB0 29 2A 2B 2C 2D 2E 2F 30 31 32 33 7F 7F 7F 7F 7F )*+,-./0123.....
也可以猜测是base64相关的操作
4.脚本解密
import base64 str1='you_know_how_to_remove_junk_code' flag='' for i in str1: flag += chr(ord(i)^0x25) print(base64.b64encode(flag))
5.get flag!
XEpQek5LSlJ6TUpSelFKeldASEpTQHpPUEtOekZKQUA=
