1、简介
iptables是linux/unix自带的一款开源基于包过滤的防火墙工具,使用非常灵活,对硬件资源需求不是很高,是在内核中集成的服务,主要工作在OSI的二、三、四层。
术语介绍:
Netfilter:是表的容器 表:链的容器 链:规则的容器 规则:iptables一系列过滤信息的规范和具体方法
工作流程:
客户端请求数据------》iptables Filter-------》获取主机的服务(直接拒绝Drop)
数据包————过滤规则 1————过滤规则 2————默认规则 拒绝就 Drop--------------------------------后面的规则不起作用 没有匹配————拒绝就 Drop--------------后面的规则不起作用 前两个规则都没有匹配—————默认规则去过滤
防火墙是层层过滤,数据包的匹配规则是自上而下顺序匹配,如果前面都没有匹配上规则(这个匹配规则是无论通过还是拒绝都是匹配上规则),明确通过或阻止,最后交给防火墙默认规则去处理
2、常用表的介绍
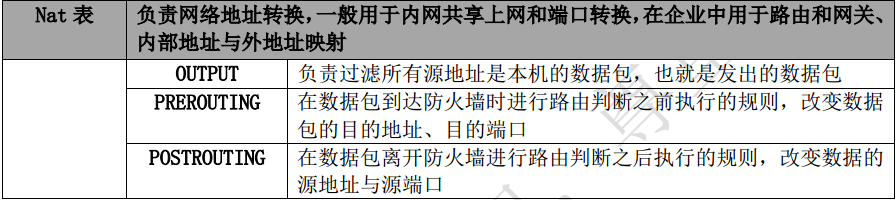
常用的表有:filter、nat、mangle
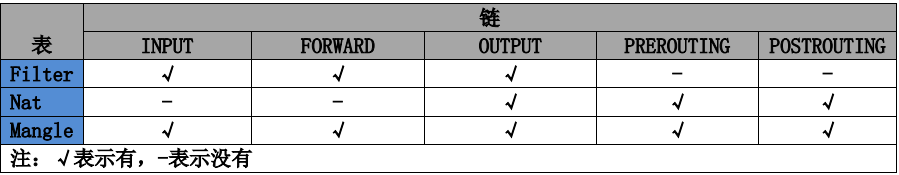

完整过程:
1、数据包进入----经过NAT PREROUTING----经过 FORWARD----FILTER INPUT----NAT OUTPUT----FILTER OUTPUT----NAT POSTROUTING 主要用于NAT或端口映射
2、数据包经过----经过 FORWARD----FILTER FORWARD----NAT POSTROUTING 主要用于过滤
3、帮助信息
[root@VM_0_7_centos ~]# iptables -h
iptables v1.4.7
Usage: iptables -[ACD] chain rule-specification [options]
iptables -I chain [rulenum] rule-specification [options]
iptables -R chain rulenum rule-specification [options]
iptables -D chain rulenum [options]
iptables -[LS] [chain [rulenum]] [options]
iptables -[FZ] [chain] [options]
iptables -[NX] chain
iptables -E old-chain-name new-chain-name
iptables -P chain target [options]
iptables -h (print this help information)
Commands:
Either long or short options are allowed.
--append -A chain Append to chain 把规则添加到链的结尾
--check -C chain Check for the existence of a rule
--delete -D chain Delete matching rule from chain 删除匹配规则从链中
--delete -D chain rulenum
Delete rule rulenum (1 = first) from chain
--insert -I chain [rulenum]
Insert in chain as rulenum (default 1=first) 把规则添加到链的开头
--replace -R chain rulenum
Replace rule rulenum (1 = first) in chain
--list -L [chain [rulenum]]
List the rules in a chain or all chains #以列表的形式查看
--list-rules -S [chain [rulenum]]
Print the rules in a chain or all chains
--flush -F [chain] Delete all rules in chain or all chains #清除所有规则
--zero -Z [chain [rulenum]]
Zero counters in chain or all chains #清除计数器
--new -N chain Create a new user-defined chain #以数字的形式查看
--delete-chain
-X [chain] Delete a user-defined chain #清除用户自定义链
--policy -P chain target
Change policy on chain to target #将链策略更改为目标
--rename-chain
-E old-chain new-chain
Change chain name, (moving any references)
Options:
[!] --proto -p proto protocol: by number or name, eg. `tcp' 指定端口类型,如tcp,udp
[!] --source -s address[/mask][...]
source specification 原规则(-s 后面跟IP地址)
[!] --destination -d address[/mask][...]
destination specification
[!] --in-interface -i input name[+]
network interface name ([+] for wildcard) 网络接口名称(后面跟网络接口,如eth0)
--jump -j target
target for rule (may load target extension) 目标规则
--goto -g chain
jump to chain with no return
--match -m match
extended match (may load extension)
--numeric -n numeric output of addresses and ports #端口和地址的数字输出
[!] --out-interface -o output name[+]
network interface name ([+] for wildcard) 网络接口名称(是output的网络接口名称,和-i区别开来)
--table -t table table to manipulate (default: `filter') #指定表
--verbose -v verbose mode
--line-numbers print line numbers when listing
--exact -x expand numbers (display exact values)
[!] --fragment -f match second or further fragments only
--modprobe=<command> try to insert modules using this command
--set-counters PKTS BYTES set the counter during insert/append
[!] --version -V print package version.
[root@VM_0_7_centos ~]# /etc/init.d/iptables status 查看iptables的运行状态 Table: filter Chain INPUT (policy ACCEPT) num target prot opt source destination Chain FORWARD (policy ACCEPT) num target prot opt source destination Chain OUTPUT (policy ACCEPT) num target prot opt source destination [root@VM_0_7_centos ~]# iptables -L -n 查看表列表和端口地址 Chain INPUT (policy ACCEPT) target prot opt source destination Chain FORWARD (policy ACCEPT) target prot opt source destination Chain OUTPUT (policy ACCEPT) target prot opt source destination
清除规则
[root@VM_0_7_centos ~]# iptables -F 清除iptables规则 [root@VM_0_7_centos ~]# iptables -L Chain INPUT (policy ACCEPT) target prot opt source destination Chain FORWARD (policy ACCEPT) target prot opt source destination Chain OUTPUT (policy ACCEPT) target prot opt source destination
清除指定表 iptablers -F -t 表名
[root@VM_0_7_centos ~]# iptables -t filter -A INPUT -p tcp --dport 22 -j DROP
因为默认的是filter表,所以和iptables -F一样
配置防火墙前最好写一个定时任务,每多长时间就关闭防火墙,这样就可以防止无法远程登录
-A 把规则添加到链的结尾
-I 把规则添加到链的开头
[root@VM_0_7_centos ~]# iptables -t filter -A INPUT -p tcp --dport 9001 -j DROP [root@VM_0_7_centos ~]# iptables -t filter -A INPUT -p tcp --dport 9002 -j DROP [root@VM_0_7_centos ~]# /etc/init.d/iptables status Table: filter Chain INPUT (policy ACCEPT) num target prot opt source destination 1 DROP tcp -- 0.0.0.0/0 0.0.0.0/0 tcp dpt:9001 2 DROP tcp -- 0.0.0.0/0 0.0.0.0/0 tcp dpt:9002 Chain FORWARD (policy ACCEPT) num target prot opt source destination Chain OUTPUT (policy ACCEPT) num target prot opt source destination [root@VM_0_7_centos ~]# iptables -L -n Chain INPUT (policy ACCEPT) target prot opt source destination DROP tcp -- 0.0.0.0/0 0.0.0.0/0 tcp dpt:9001 DROP tcp -- 0.0.0.0/0 0.0.0.0/0 tcp dpt:9002 Chain FORWARD (policy ACCEPT) target prot opt source destination Chain OUTPUT (policy ACCEPT) target prot opt source destination
在实际的企业应用中,如果默认的规则是允许的,但是我又得禁止某一个应用或服务时,就会用到-I参数,将规则放在最前面,比如你发现一个网站被一个IP频繁访问,就可以用它来禁止
[root@VM_0_7_centos ~]# iptables -t filter -I INPUT -p tcp -s 10.0.100.1 --dport 9003 -j ACCEPT [root@VM_0_7_centos ~]# /etc/init.d/iptables status Table: filter Chain INPUT (policy ACCEPT) num target prot opt source destination 1 ACCEPT tcp -- 10.0.100.1 0.0.0.0/0 tcp dpt:9003 2 DROP tcp -- 0.0.0.0/0 0.0.0.0/0 tcp dpt:9001 3 DROP tcp -- 0.0.0.0/0 0.0.0.0/0 tcp dpt:9002 Chain FORWARD (policy ACCEPT) num target prot opt source destination Chain OUTPUT (policy ACCEPT) num target prot opt source destination
删除某一行规则
[root@VM_0_7_centos ~]# /etc/init.d/iptables status Table: filter Chain INPUT (policy ACCEPT) num target prot opt source destination 1 ACCEPT tcp -- 10.0.100.1 0.0.0.0/0 tcp dpt:9003 2 DROP tcp -- 0.0.0.0/0 0.0.0.0/0 tcp dpt:9001 3 DROP tcp -- 0.0.0.0/0 0.0.0.0/0 tcp dpt:9002 Chain FORWARD (policy ACCEPT) num target prot opt source destination Chain OUTPUT (policy ACCEPT) num target prot opt source destination [root@VM_0_7_centos ~]# iptables -D INPUT 3 [root@VM_0_7_centos ~]# /etc/init.d/iptables status Table: filter Chain INPUT (policy ACCEPT) num target prot opt source destination 1 ACCEPT tcp -- 10.0.100.1 0.0.0.0/0 tcp dpt:9003 2 DROP tcp -- 0.0.0.0/0 0.0.0.0/0 tcp dpt:9001 Chain FORWARD (policy ACCEPT) num target prot opt source destination Chain OUTPUT (policy ACCEPT) num target prot opt source destination
禁止某网段的流量
[root@VM_0_7_centos ~]# iptables -A INPUT -i eth0 -s 10.0.0.0/24 -j DROP
[root@VM_0_7_centos ~]# /etc/init.d/iptables status Table: filter Chain INPUT (policy ACCEPT) num target prot opt source destination 1 ACCEPT tcp -- 10.0.100.1 0.0.0.0/0 tcp dpt:9003 2 DROP tcp -- 0.0.0.0/0 0.0.0.0/0 tcp dpt:9001 3 DROP all -- 10.0.0.0/24 0.0.0.0/0 Chain FORWARD (policy ACCEPT) num target prot opt source destination Chain OUTPUT (policy ACCEPT) num target prot opt source destination
iptables企业级应用配置
清除规则
[root@VM_0_7_centos ~]# iptables -F [root@VM_0_7_centos ~]# iptables -X [root@VM_0_7_centos ~]# iptables -Z [root@VM_0_7_centos ~]# /etc/init.d/iptables status Table: filter Chain INPUT (policy ACCEPT) num target prot opt source destination Chain FORWARD (policy ACCEPT) num target prot opt source destination Chain OUTPUT (policy ACCEPT) num target prot opt source destination
配置规则使得内网用户可用
[root@VM_0_7_centos ~]# iptables -A INPUT -s 100.1.3.9/24 -j ACCEPT [root@VM_0_7_centos ~]# iptables -A INPUT -p tcp --dport 22 -j ACCEPT [root@VM_0_7_centos ~]# iptables -A INPUT -i lo -j ACCEPT [root@VM_0_7_centos ~]# iptables -A OUTPUT -o lo -j ACCEPT
设置规则(默认规则)
[root@VM_0_7_centos ~]# iptables -P INPUT DROP [root@VM_0_7_centos ~]# iptables -P FORWARD DROP [root@VM_0_7_centos ~]# iptables -P OUTPUT DROP
配置用户访问web页面(这个不能禁止,因为网站是开放给全球用户访问)
[root@VM_0_7_centos ~]# iptables -t filter -A INPUT -p tcp --dport 80 -j ACCEPT [root@VM_0_7_centos ~]# /etc/init.d/iptables status Table: filter Chain INPUT (policy ACCEPT) num target prot opt source destination 1 ACCEPT tcp -- 0.0.0.0/0 0.0.0.0/0 tcp dpt:80 Chain FORWARD (policy ACCEPT) num target prot opt source destination Chain OUTPUT (policy ACCEPT) num target prot opt source destination
因为所有iptables命令都是保存在内存中的,重启计算机就会失效
[root@VM_0_7_centos ~]# cp /etc/sysconfig/iptables /etc/sysconfig/iptables.bak [root@VM_0_7_centos ~]# /etc/init.d/iptables save iptables: Saving firewall rules to /etc/sysconfig/iptables:[ OK ] 成功保存iptables规则
维护iptables防火墙
[root@VM_0_7_centos ~]# vim /etc/sysconfig/iptables # Generated by iptables-save v1.4.7 on Fri Mar 23 11:13:52 2018 *filter :INPUT ACCEPT [938:61166] :FORWARD ACCEPT [0:0] :OUTPUT ACCEPT [872:82030] -A INPUT -p tcp -m tcp --dport 80 -j ACCEPT COMMIT # Completed on Fri Mar 23 11:13:52 2018