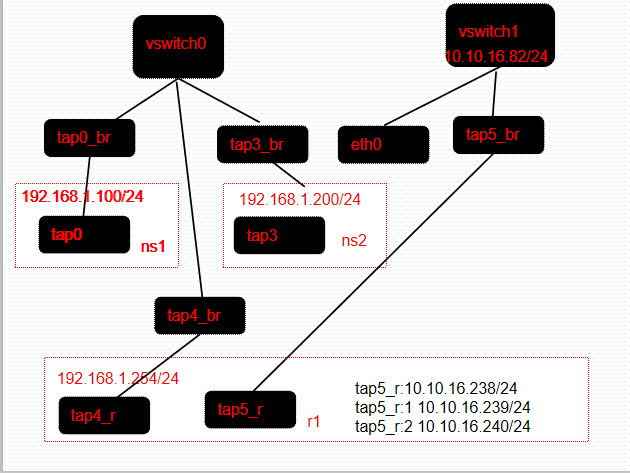
eth0连接internet
ns1
[root@kunpeng82 devuser]# ip netns exec ns1 route -n Kernel IP routing table Destination Gateway Genmask Flags Metric Ref Use Iface 0.0.0.0 192.168.1.254 0.0.0.0 UG 0 0 0 tap0 192.168.1.0 0.0.0.0 255.255.255.0 U 0 0 0 tap0
ns2
[root@kunpeng82 devuser]# ip netns exec ns2 route -n Kernel IP routing table Destination Gateway Genmask Flags Metric Ref Use Iface 0.0.0.0 192.168.1.254 0.0.0.0 UG 0 0 0 tap3 192.168.1.0 0.0.0.0 255.255.255.0 U 0 0 0 tap3 [root@kunpeng82 devuser]#
r1
[root@kunpeng82 devuser]# ip netns exec r1 route -n Kernel IP routing table Destination Gateway Genmask Flags Metric Ref Use Iface 0.0.0.0 10.10.16.82 0.0.0.0 UG 0 0 0 tap5_r 10.10.16.0 0.0.0.0 255.255.255.0 U 0 0 0 tap5_r 192.168.1.0 0.0.0.0 255.255.255.0 U 0 0 0 tap4_r [root@kunpeng82 devuser]#
[root@kunpeng82 devuser]# ip netns exec r1 ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
24: tap4_r@if23: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP group default qlen 1000
link/ether 22:72:23:d0:7d:7c brd ff:ff:ff:ff:ff:ff link-netnsid 0
inet 192.168.1.254/24 scope global tap4_r
valid_lft forever preferred_lft forever
inet6 fe80::2072:23ff:fed0:7d7c/64 scope link
valid_lft forever preferred_lft forever
26: tap5_r@if25: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP group default qlen 1000
link/ether 3e:d7:c5:49:ed:19 brd ff:ff:ff:ff:ff:ff link-netnsid 0
inet 10.10.16.238/24 scope global tap5_r
valid_lft forever preferred_lft forever
inet 10.10.16.239/24 brd 10.10.16.255 scope global secondary tap5_r:1
valid_lft forever preferred_lft forever
inet 10.10.16.240/24 brd 10.10.16.255 scope global secondary tap5_r:2
valid_lft forever preferred_lft forever
添加nat规则
ip netns exec r1 ip addr add 10.10.16.238/24 dev tap5_r
#创建两个浮动ip
ip netns exec r1 ifconfig tap5_r:1 10.10.16.239/24 up
ip netns exec r1 ifconfig tap5_r:2 10.10.16.240/24 up
#配置ns1、ns2的网关
ip netns exec r1 ip addr add 192.168.1.254/24 dev tap4_r
#给r1添加默认网关
ip netns exec r1 ip r add default via 10.10.16.82 dev tap5_r
#开启ip forward,这样从tap4收到的数据包如果需要转发,能通过tap5转发
ip netns exec r1 sysctl -w net.ipv4.ip_forward=1
ip netns exec r1 iptables -t nat -A POSTROUTING -s 192.168.1.100/32 -j SNAT --to-source 10.10.16.239 ip netns exec r1 iptables -t nat -A PREROUTING -d 10.10.16.239/32 -j DNAT --to-destination 192.168.1.100 ip netns exec r1 iptables -t nat -A POSTROUTING -s 192.168.1.200/32 -j SNAT --to-source 10.10.16.240 ip netns exec r1 iptables -t nat -A PREROUTING -d 10.10.16.240/32 -j DNAT --to-destination 192.168.1.200
[root@kunpeng82 devuser]# ip netns exec ns2 ping 8.8.8.8 PING 8.8.8.8 (8.8.8.8) 56(84) bytes of data. 64 bytes from 8.8.8.8: icmp_seq=1 ttl=42 time=16.5 ms 64 bytes from 8.8.8.8: icmp_seq=2 ttl=43 time=14.2 ms ^C --- 8.8.8.8 ping statistics --- 2 packets transmitted, 2 received, 0% packet loss, time 1001ms rtt min/avg/max/mdev = 14.267/15.409/16.552/1.149 ms [root@kunpeng82 devuser]# ip netns exec ns1 ping 8.8.8.8 PING 8.8.8.8 (8.8.8.8) 56(84) bytes of data. 64 bytes from 8.8.8.8: icmp_seq=1 ttl=42 time=16.5 ms 64 bytes from 8.8.8.8: icmp_seq=2 ttl=44 time=13.4 ms ^C --- 8.8.8.8 ping statistics --- 2 packets transmitted, 2 received, 0% packet loss, time 1001ms rtt min/avg/max/mdev = 13.439/14.979/16.519/1.540 ms
ping 10.10.16.239,同时在tap0_br上执行tcpdump
[root@kunpeng82 devuser]# ping 10.10.16.239 PING 10.10.16.239 (10.10.16.239) 56(84) bytes of data. 64 bytes from 10.10.16.239: icmp_seq=1 ttl=63 time=0.528 ms 64 bytes from 10.10.16.239: icmp_seq=2 ttl=63 time=0.050 ms ^C --- 10.10.16.239 ping statistics --- 2 packets transmitted, 2 received, 0% packet loss, time 1071ms rtt min/avg/max/mdev = 0.050/0.289/0.528/0.239 ms [root@kunpeng82 devuser]#
[root@kunpeng82 devuser]# tcpdump -i tap0_br -nnvv
tcpdump: listening on tap0_br, link-type EN10MB (Ethernet), capture size 262144 bytes
08:13:32.035608 IP (tos 0x0, ttl 63, id 58630, offset 0, flags [DF], proto ICMP (1), length 84)
10.10.16.82 > 192.168.1.100: ICMP echo request, id 6540, seq 1, length 64
08:13:32.035634 IP (tos 0x0, ttl 64, id 19752, offset 0, flags [none], proto ICMP (1), length 84)
192.168.1.100 > 10.10.16.82: ICMP echo reply, id 6540, seq 1, length 64
08:13:33.107164 IP (tos 0x0, ttl 63, id 58700, offset 0, flags [DF], proto ICMP (1), length 84)
10.10.16.82 > 192.168.1.100: ICMP echo request, id 6540, seq 2, length 64
08:13:33.107181 IP (tos 0x0, ttl 64, id 19847, offset 0, flags [none], proto ICMP (1), length 84)
192.168.1.100 > 10.10.16.82: ICMP echo reply, id 6540, seq 2, length 64
08:13:37.107140 ARP, Ethernet (len 6), IPv4 (len 4), Request who-has 192.168.1.254 tell 192.168.1.100, length 28
08:13:37.107342 ARP, Ethernet (len 6), IPv4 (len 4), Reply 192.168.1.254 is-at 22:72:23:d0:7d:7c, length 28
ping 10.10.16.239 的icmp request报文经过r1时r1上执行了这条规则
ip netns exec r1 iptables -t nat -A PREROUTING -d 10.10.16.239/32 -j DNAT --to-destination 192.168.1.100
192.168.1.100的reply报文经过r1时r1上执行了这条规则
ip netns exec r1 iptables -t nat -A POSTROUTING -s 192.168.1.100/32 -j SNAT --to-source 10.10.16.239