1.flag_in_your_hand && flag_in_your_hand1
下载,解压后
![]()
打开index文件,直接点击get flag错误,输入其他点击也同样
打开js文件,在其中找到正确的Token条件
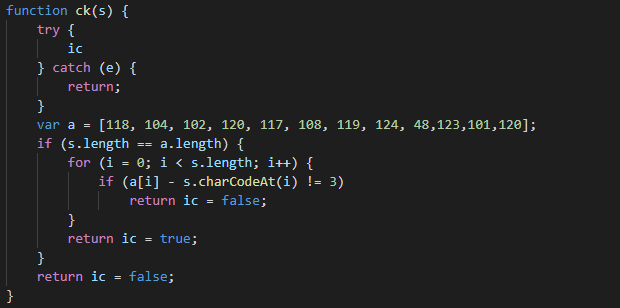
可知Token里要填的是a数列里的ASCII码得到的字符,代码如下:
a=[118, 104, 102, 120, 117, 108, 119, 124, 48, 123, 101, 120]
b=list()
for i in a:
i=i-3
b.append(chr(i))
s=''
for i in b:
s+=i
print(s)
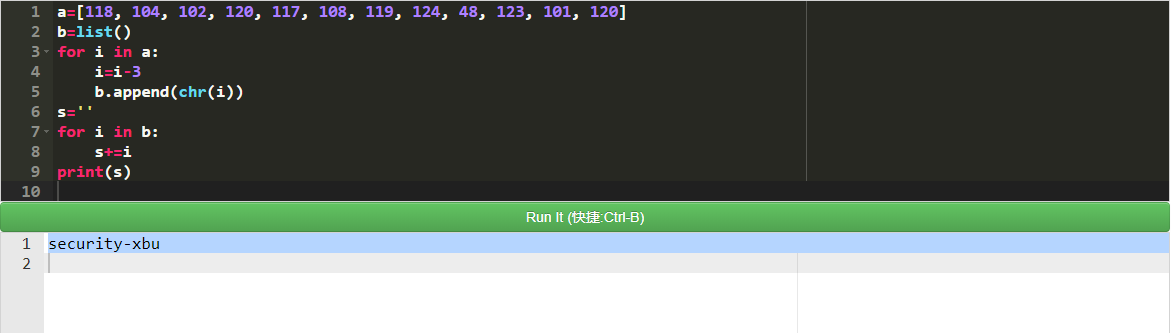
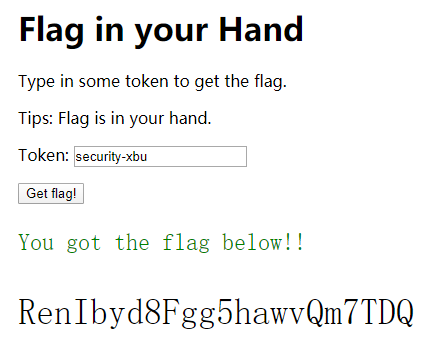
在Token里输入得到结果security-xbu,得到flag
2.告诉你个秘密
是一个TXT文件,下载好之后,内容如下
![]()
16进制转成字符串
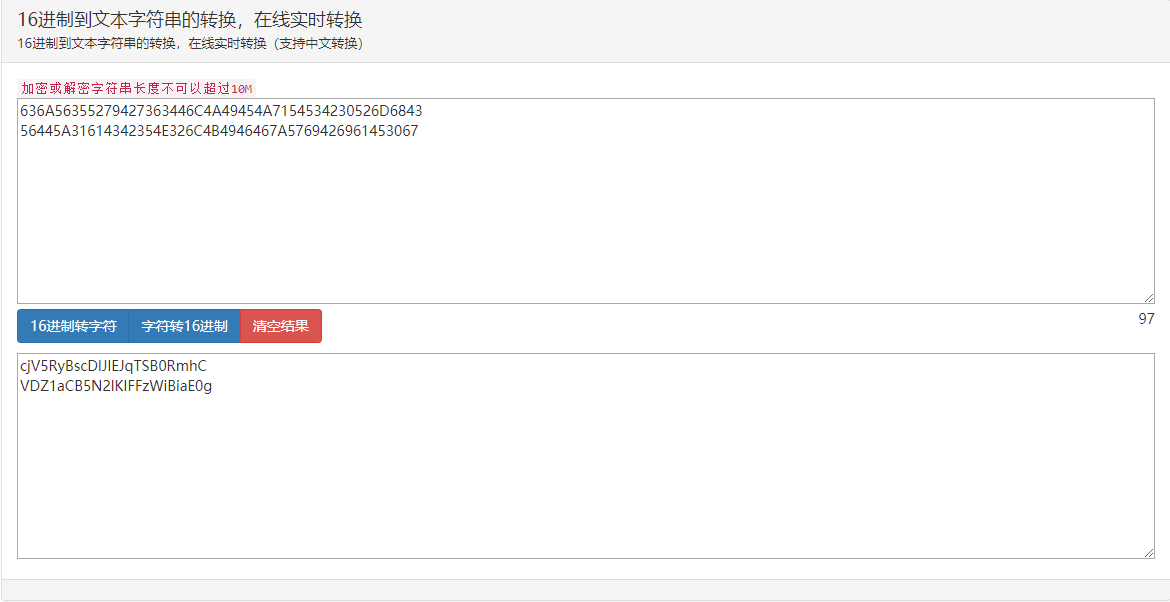
然后base64解码
键盘加密:一组字符在键盘上所圈住的字母就是加密内容
连在一起,得到flag(记得大写)
3.Broadcast
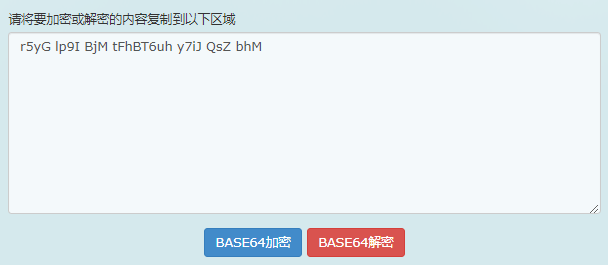
下载之后是一堆文件
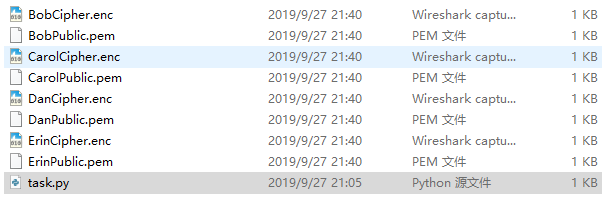
用记事本或者编辑器打开task.py(这里我用的是Notepad++),得flag
4.cr3-what-is-this-encryption
看到p,q,e,c,就知道是RSA加密,脚本解密:
import libnum
from Crypto.Util.number import long_to_bytes
c = 0x7fe1a4f743675d1987d25d38111fae0f78bbea6852cba5beda47db76d119a3efe24cb04b9449f53becd43b0b46e269826a983f832abb53b7a7e24a43ad15378344ed5c20f51e268186d24c76050c1e73647523bd5f91d9b6ad3e86bbf9126588b1dee21e6997372e36c3e74284734748891829665086e0dc523ed23c386bb520
e = int("0x6d1fdab4ce3217b3fc32c9ed480a31d067fd57d93a9ab52b472dc393ab7852fbcb11abbebfd6aaae8032db1316dc22d3f7c3d631e24df13ef23d3b381a1c3e04abcc745d402ee3a031ac2718fae63b240837b4f657f29ca4702da9af22a3a019d68904a969ddb01bcf941df70af042f4fae5cbeb9c2151b324f387e525094c41",16)
q = int("0xa6055ec186de51800ddd6fcbf0192384ff42d707a55f57af4fcfb0d1dc7bd97055e8275cd4b78ec63c5d592f567c66393a061324aa2e6a8d8fc2a910cbee1ed9",16)
p = int("0xfa0f9463ea0a93b929c099320d31c277e0b0dbc65b189ed76124f5a1218f5d91fd0102a4c8de11f28be5e4d0ae91ab319f4537e97ed74bc663e972a4a9119307",16)
n = q*p
d = libnum.invmod(e, (p - 1) * (q - 1))
m = pow(c, d, n) # m 的十进制形式
string = long_to_bytes(m) # m明文
print(string) # 结果为 b‘ m ’ 的形式
得到flag:ALEXCTF{RS4_I5_E55ENT1AL_T0_D0_BY_H4ND}
5.工业协议分析2
![]()
用Wireshark打开,发现大量的UPD包,仔细分析后发现大量的upd包大小都一样,只有少量的是不同的,一个一个找下去,发现如下包有异常字符
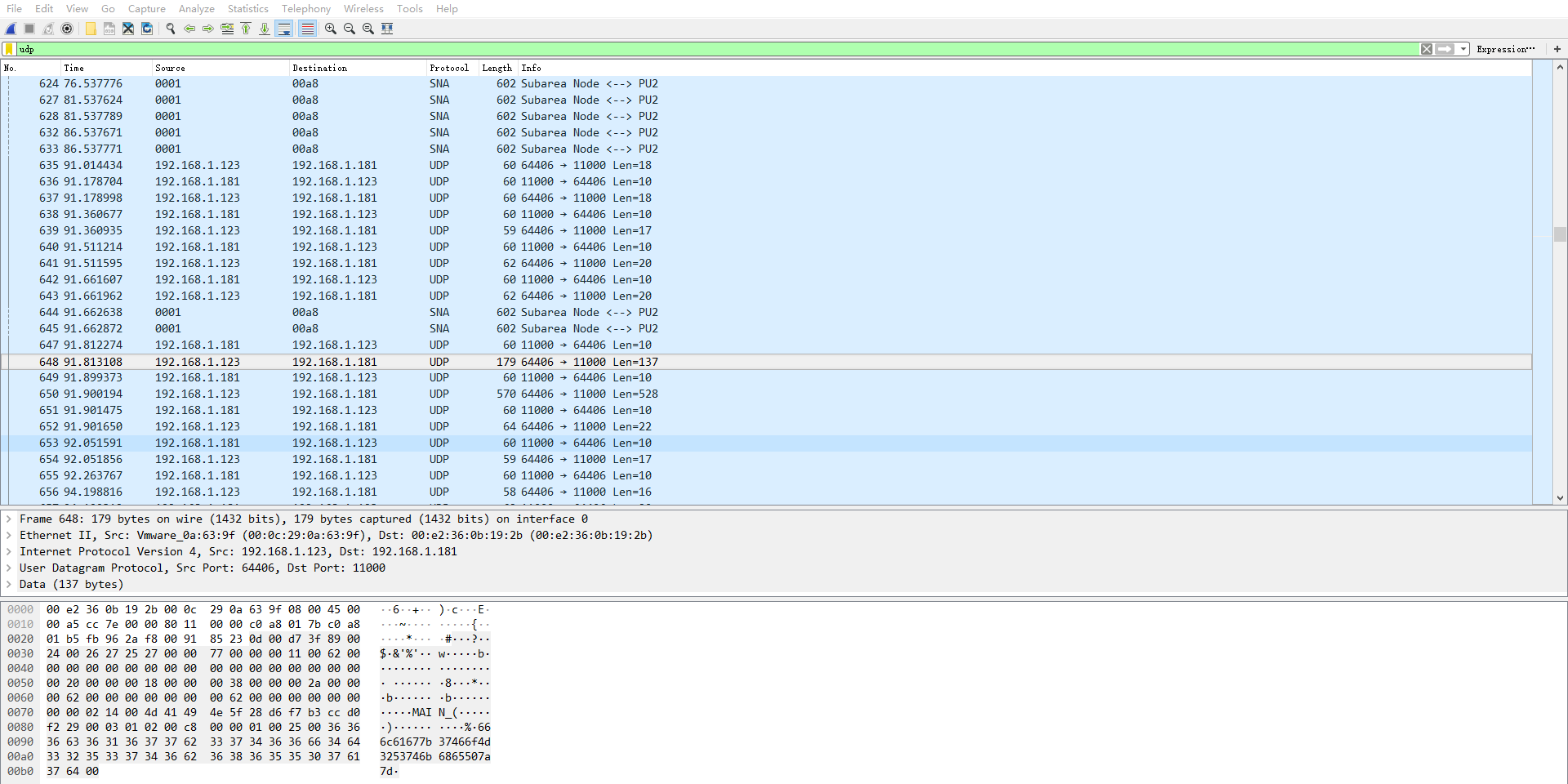
将字符拿出来,ASCII码解密,得到flag
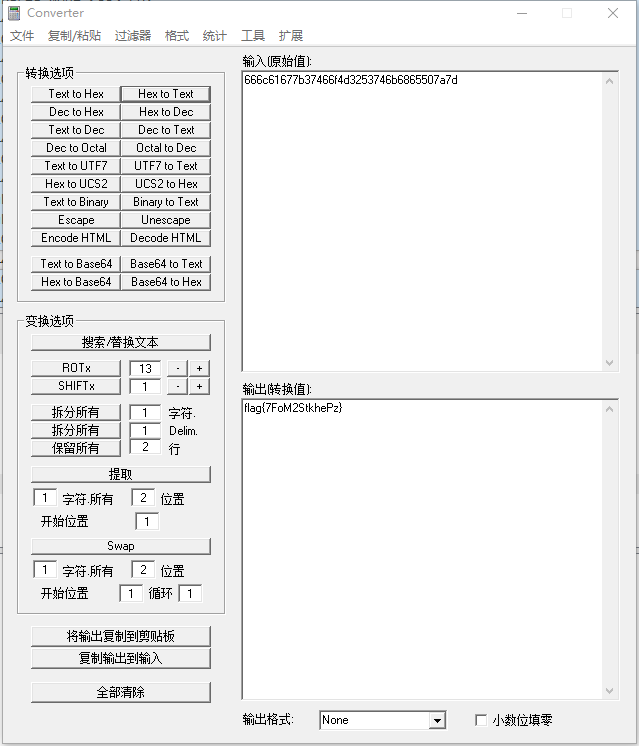
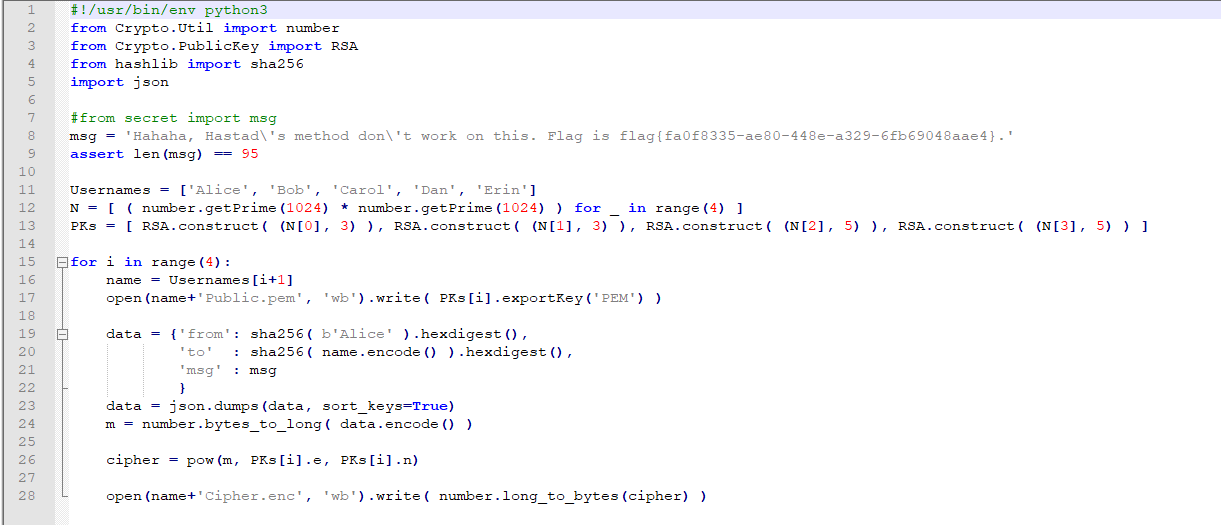
6.你猜猜
下载打开后,前几位明显是zip文件头

HxD新建文件,将txt里的内容拷贝进去,保存为zip文件
![]()
打开之后发现需要密码,暴力破解得到密码

输入密码,得到flag.txt文件,打开就是flag
7.Safer-than-rot13
记事本打开,得到大量字符串
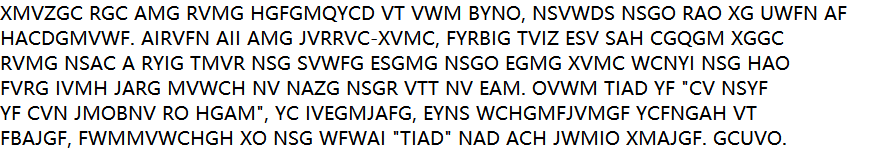
然后去quipqiup网站上进行解码
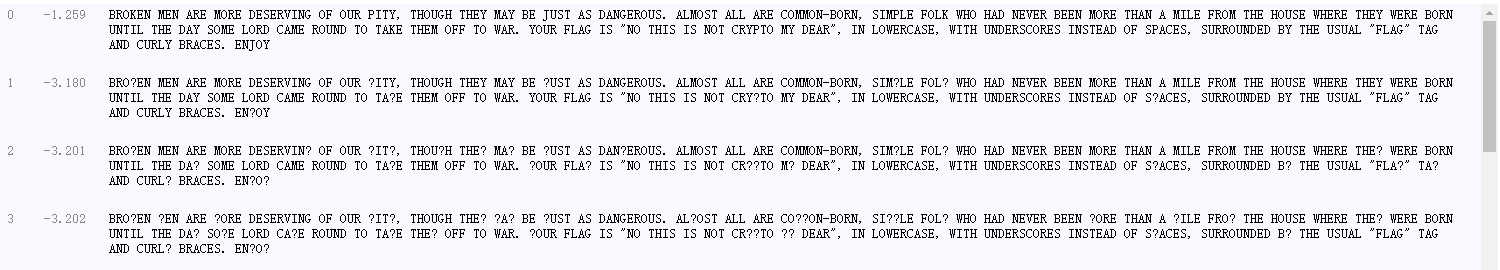
最后把空格换成下划线,大写字母变成小写,得到flag
8.shanghai
题目提示:维吉尼亚密码,
所以直接上网站解密就行了https://guballa.de/vigenere-solver
得到flag
9.OldDriver
打开发现给了10组RSA加密信息

贴脚本
import libnum
import gmpy2
dic = [{"c": 7366067574741171461722065133242916080495505913663250330082747465383676893970411476550748394841437418105312353971095003424322679616940371123028982189502042, "e": 10, "n": 25162507052339714421839688873734596177751124036723831003300959761137811490715205742941738406548150240861779301784133652165908227917415483137585388986274803},
{"c": 21962825323300469151795920289886886562790942771546858500842179806566435767103803978885148772139305484319688249368999503784441507383476095946258011317951461, "e": 10, "n": 23976859589904419798320812097681858652325473791891232710431997202897819580634937070900625213218095330766877190212418023297341732808839488308551126409983193},
{"c": 6569689420274066957835983390583585286570087619048110141187700584193792695235405077811544355169290382357149374107076406086154103351897890793598997687053983, "e": 10, "n": 18503782836858540043974558035601654610948915505645219820150251062305120148745545906567548650191832090823482852604346478335353784501076761922605361848703623},
{"c": 4508246168044513518452493882713536390636741541551805821790338973797615971271867248584379813114125478195284692695928668946553625483179633266057122967547052, "e": 10, "n": 23383087478545512218713157932934746110721706819077423418060220083657713428503582801909807142802647367994289775015595100541168367083097506193809451365010723},
{"c": 22966105670291282335588843018244161552764486373117942865966904076191122337435542553276743938817686729554714315494818922753880198945897222422137268427611672, "e": 10, "n": 31775649089861428671057909076144152870796722528112580479442073365053916012507273433028451755436987054722496057749731758475958301164082755003195632005308493},
{"c": 17963313063405045742968136916219838352135561785389534381262979264585397896844470879023686508540355160998533122970239261072020689217153126649390825646712087, "e": 10, "n": 22246342022943432820696190444155665289928378653841172632283227888174495402248633061010615572642126584591103750338919213945646074833823905521643025879053949},
{"c": 1652417534709029450380570653973705320986117679597563873022683140800507482560482948310131540948227797045505390333146191586749269249548168247316404074014639, "e": 10, "n": 25395461142670631268156106136028325744393358436617528677967249347353524924655001151849544022201772500033280822372661344352607434738696051779095736547813043},
{"c": 15585771734488351039456631394040497759568679429510619219766191780807675361741859290490732451112648776648126779759368428205194684721516497026290981786239352, "e": 10, "n": 32056508892744184901289413287728039891303832311548608141088227876326753674154124775132776928481935378184756756785107540781632570295330486738268173167809047},
{"c": 8965123421637694050044216844523379163347478029124815032832813225050732558524239660648746284884140746788823681886010577342254841014594570067467905682359797, "e": 10, "n": 52849766269541827474228189428820648574162539595985395992261649809907435742263020551050064268890333392877173572811691599841253150460219986817964461970736553},
{"c": 13560945756543023008529388108446940847137853038437095244573035888531288577370829065666320069397898394848484847030321018915638381833935580958342719988978247, "e": 10, "n": 30415984800307578932946399987559088968355638354344823359397204419191241802721772499486615661699080998502439901585573950889047918537906687840725005496238621}]
n = []
C = []
for i in dic:
n.append(i["n"])
C.append(i["c"])
# for i in n:
# for j in n:
# if i == j:
# continue
# else:
# if gmpy2.gcd(i, j) != 1:
# print i, j
N = 1
for i in n:
N *= i
Ni = []
for i in n:
Ni.append(N / i)
T = []
for i in xrange(10):
T.append(long(gmpy2.invert(Ni[i], n[i])))
X = 0
for i in xrange(10):
X += C[i] * Ni[i] * T[i]
m10 = X % N
m = gmpy2.iroot(m10, 10)
print libnum.n2s(m[0])
运行,得flag:flag{wo0_th3_tr4in_i5_leav1ng_g3t_on_it}
10.工控安全取证
拿到文件,改成Wireshark可以识别的文件后缀(.pcapng)

分析流量包发现存在ICMP、TCP、UDP协议的流量包,其中IP地址192.168.0.9向IP地址192.168.0.99发送大量的TCP请求,题目要求分析第四次发起扫描时的数据包,如果一个一个审计TCP的连接请求工作量太大,于是换一个思路,观察数据包发现,一开始,IP地址192.168.0.9向IP地址192.168.0.99发送了一个ICMP的Ping请求,之后才是大量的TCP请求数据。于是,猜测在每次发送TCP请求,会先进行一次ICMP的Ping请求。于是,在Wireshark中过滤出ICMP的数据包进行分析,然后分析其中ICMP的数据包编号。
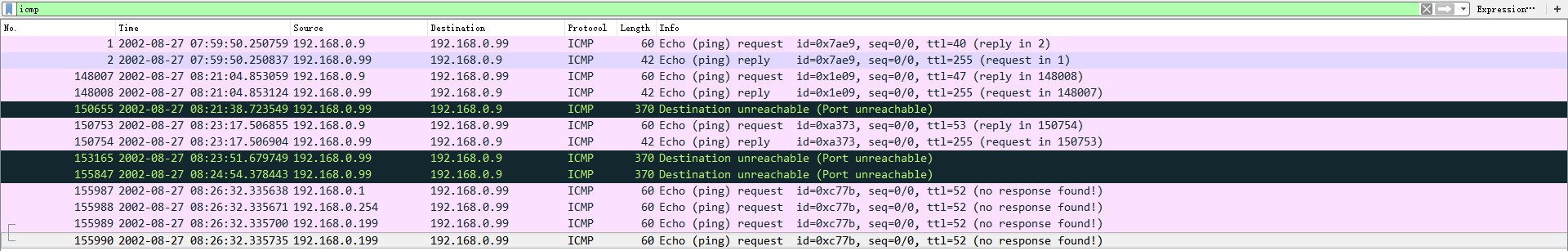
最终发现IP为192.168.0.199的ICMP的Ping请求对应的数据包编号155989和155990,尝试之后发现flag为155989
11.fanfie
(这道题是真的没想出来,百度一下大佬的Writeup,哇,脑回路是真的新奇= =||)
首先对BITSCTF进行base32加密后得到的是:IJEVIU2DKRDA====
与密文前面几位进行对应,发现:M解密两次对应的都是I,不同的字母对应的都是不同的解密字母,那么猜测可能是根据某种规则进行了字母替换。
MZYVMIWLGBL7CIJOGJQVOA3IN5BLYC3NHI
IJEVIU2DKRDA====
对字母表进行编码:
1 A B C D E F G H I J K L M N O P Q R S T U V W X Y Z 2 3 4 5 6 7
2 0 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31
则有:3 → 11;4 → 24;8 → 12……
那么,观察可得,这是仿射密码,https://www.cnblogs.com/zishu/p/8650214.html(不懂的可以去这个博客看看,简单明了)
加密函数:E(x) = (ax + b) (mod m),其中 a与b互质,m是编码系统中字母的个数(通常都是26)。
解密函数:D(x) = (x - b) (mod m),其中
是 a 在
群的乘法逆元。
根据函数求出仿射密码的a = 13和b = 4,对应表如下:

则密文进行仿射解密得:
MZYVMIWLGBL7CIJOGJQVOA3IN5BLYC3NHI → IJEVIU2DKRDHWUZSKZ4VSMTUN5RDEWTNPU
然后对所得字符串进行base32解密得:BITSCTF{S2VyY2tob2Zm}
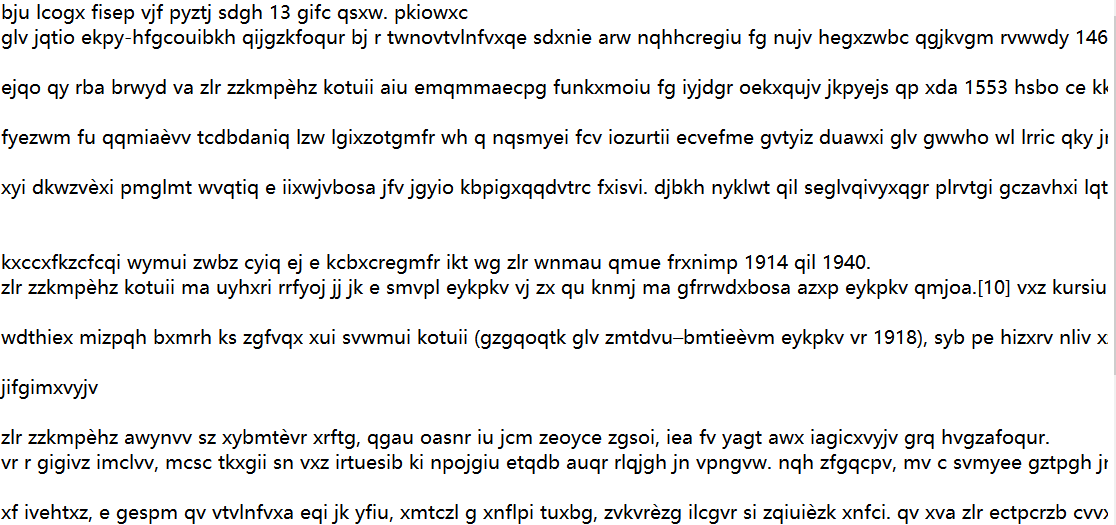
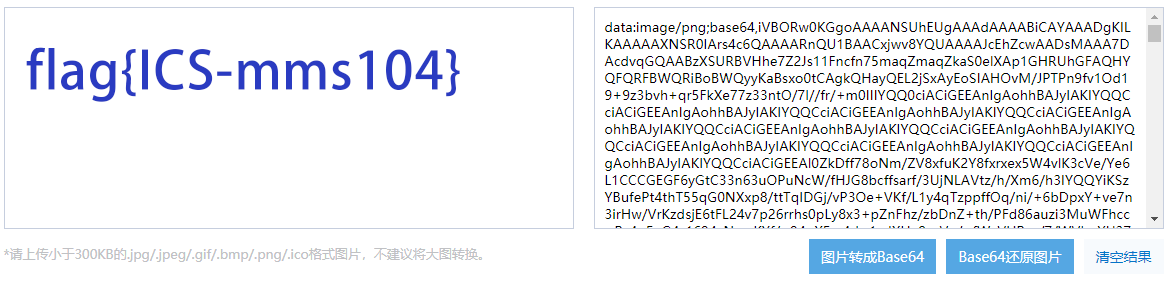
12.简单流量分析
用Wireshark打开,发现这个特殊的tcp有一串很长的base64编码

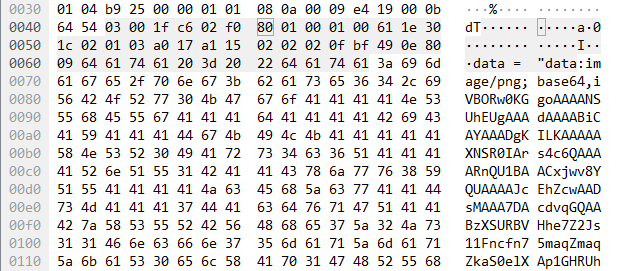
base64转图片,得到flag
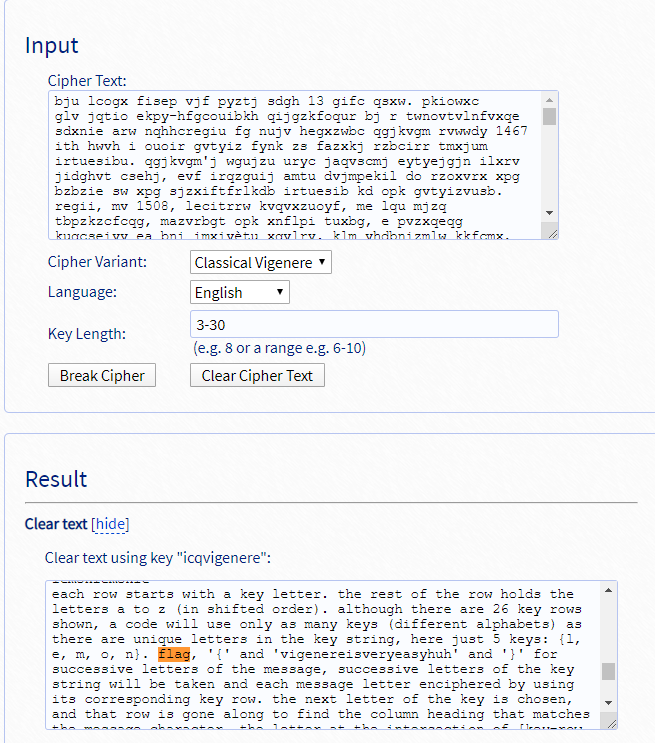
13.简单流量分析
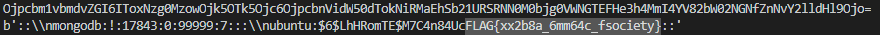
官方脚本
import pyshark import base64 L_flag = [] packets = pyshark.FileCapture('fetus_pcap.pcap') for packet in packets: for pkt in packet: if pkt.layer_name == "icmp": if int(pkt.type) != 0: L_flag.append(int(pkt.data_len)) c = len(L_flag) for i in range(0, c): L_flag[i] = chr(L_flag[i]) print(''.join(L_flag)) print(base64.b64decode(''.join(L_flag)))
运行,得到flag:flag{xx2b8a_6mm64c_fsociety}
暂时先不更新了- -||