为了完成VCSA的完整安装。需要在本地配置一台RedHat8的vm来作为本地的DNS
1.安装DNS服务
查询bind
[root@vm2 ~]# yum info bind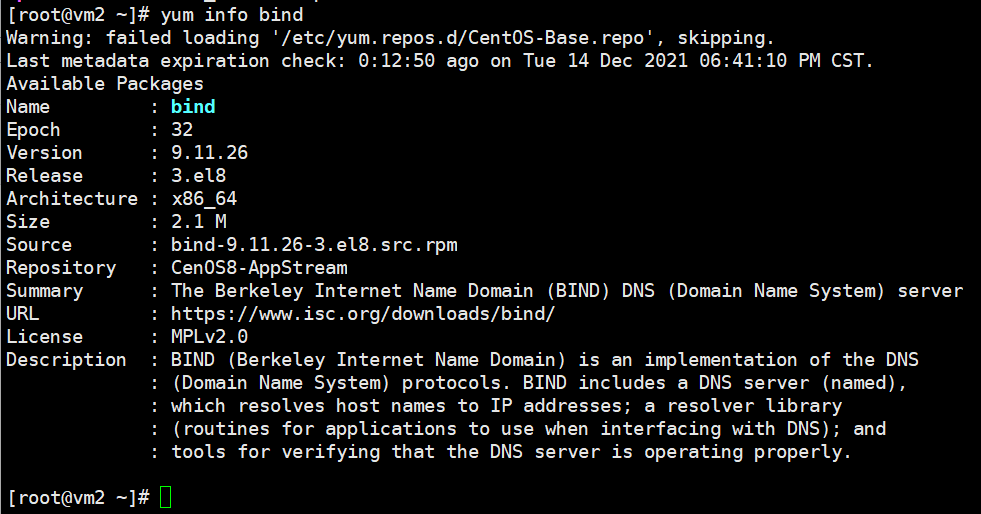
安装bind
[root@vm2 ~]# yum -y install bind
[root@vm2 ~]# rpm -ql bind
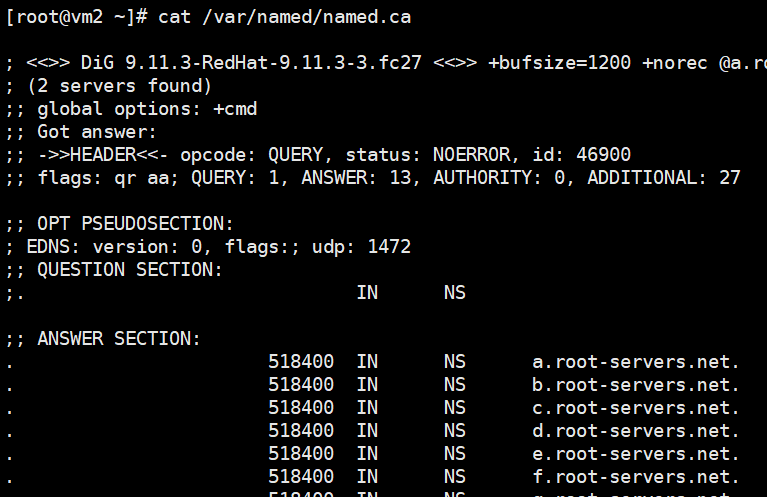
查看13个根域服务器文件:
[root@vm2 ~]# cat /var/named/named.ca
开启DNS服务,并添加防火墙端口:
[root@vm2 ~]# systemctl start named
[root@vm2 ~]# systemctl enable named
Created symlink /etc/systemd/system/multi-user.target.wants/named.service → /usr/lib/systemd/system/named.service.
[root@vm2 ~]# firewall-cmd --permanent --add-service=dns
success
[root@vm2 ~]# firewall-cmd --permanent --add-port=53/tcp
success
[root@vm2 ~]# firewall-cmd --permanent --add-port=53/udp
success
[root@vm2 ~]# firewall-cmd --reload
success
[root@vm2 ~]# ss -untl
查看修改网卡信息:
[root@vm2 ~]# vim /etc/sysconfig/network-scripts/ifcfg-ens192
PEERDNS= "no"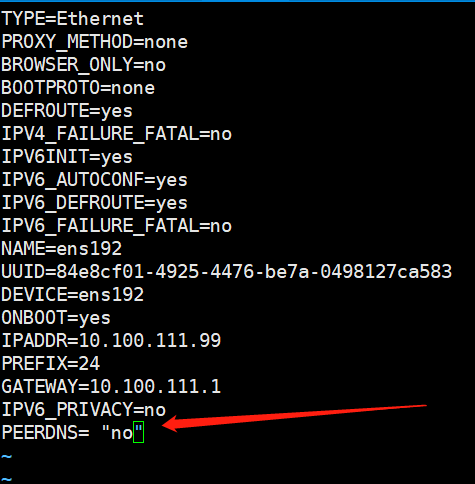
电脑重启后 /etc/resolv.conf 的namespace不会恢复至系统默认
[root@vm2 ~]# systemctl restart network-online.target
编辑DNS配置文件/etc/named.conf文件:
[root@vm2 etc]# cp -p /etc/named.conf{,.back}
[root@vm2 etc]# ll |grep named.conf
-rw-r-----. 1 root named 1705 Feb 18 2021 named.conf
-rw-r-----. 1 root named 1705 Feb 18 2021 named.conf.back
[root@vm2 etc]# vim named.conf
[root@vm2 etc]# cat named.conf // // named.conf // // Provided by Red Hat bind package to configure the ISC BIND named(8) DNS // server as a caching only nameserver (as a localhost DNS resolver only). // // See /usr/share/doc/bind*/sample/ for example named configuration files. // options { listen-on port 53 { 127.0.0.1; }; listen-on-v6 port 53 { ::1; }; directory "/var/named"; dump-file "/var/named/data/cache_dump.db"; statistics-file "/var/named/data/named_stats.txt"; memstatistics-file "/var/named/data/named_mem_stats.txt"; secroots-file "/var/named/data/named.secroots"; recursing-file "/var/named/data/named.recursing"; allow-query { localhost; }; /* - If you are building an AUTHORITATIVE DNS server, do NOT enable recursion. - If you are building a RECURSIVE (caching) DNS server, you need to enable recursion. - If your recursive DNS server has a public IP address, you MUST enable access control to limit queries to your legitimate users. Failing to do so will cause your server to become part of large scale DNS amplification attacks. Implementing BCP38 within your network would greatly reduce such attack surface */ recursion yes; dnssec-enable yes; dnssec-validation yes; managed-keys-directory "/var/named/dynamic"; pid-file "/run/named/named.pid"; session-keyfile "/run/named/session.key"; /* https://fedoraproject.org/wiki/Changes/CryptoPolicy */ include "/etc/crypto-policies/back-ends/bind.config"; }; logging { channel default_debug { file "data/named.run"; severity dynamic; }; }; zone "." IN { type hint; file "named.ca"; };
zone "example.com" IN {
type master;
file "example.com.zone";
}; include "/etc/named.rfc1912.zones"; include "/etc/named.root.key";
[root@vm2 etc]# systemctl reload named
[root@vm2 etc]# ss -ntul
[root@vm2 etc]# cat /etc/resolv.conf
# Generated by NetworkManager
search example.com