x64 分页机制——虚拟地址到物理地址寻址
原博客:http://www.cnblogs.com/lanrenxinxin/p/4735027.html
详细的理论讲解都在上面
下面说的是通过windbg手动进行寻址,深入理解
x64:
实践:
int main()
{
char* v1 = "HelloWorld";
printf("%p
", v1);
while (1)
{
}
return 0;
}
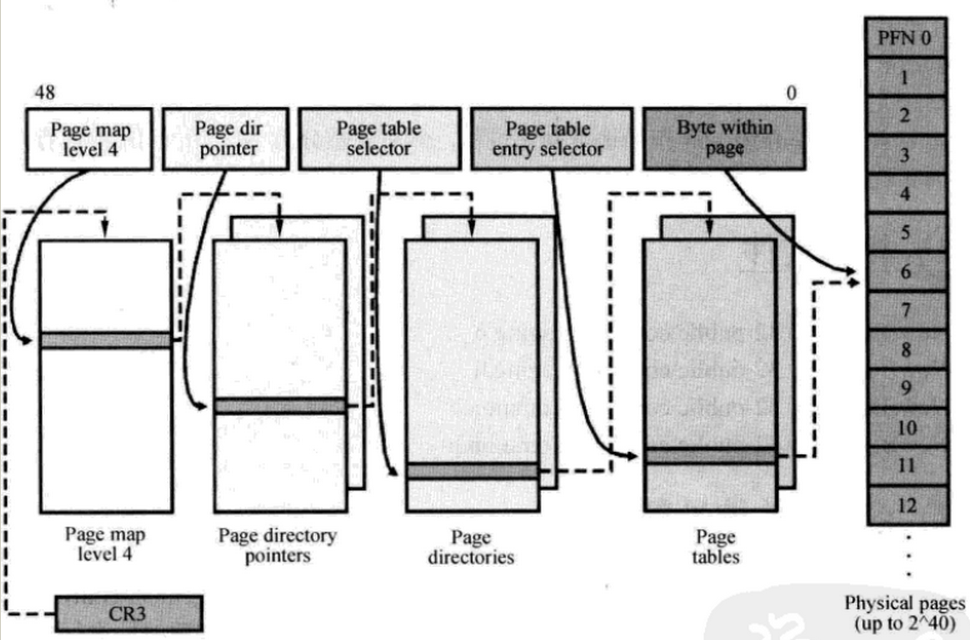
PML4T(Page Map Level4 Table)及表内的PML4E结构,每个表为4K,内含512个PML4E结构,每个8字节
PDPT (Page Directory Pointer Table)及表内的PDPTE结构,每个表4K,内含512个PDPTE结构,每个8字节
PDT (Page Directory Table)及表内的PDE结构,每个表4K,内含512个PDE结构,每个8字节
PT(Page Table)及表内额PTE结构,每个表4K,内含512个PTE结构,每个8字节。
每个table entry 的结构都是8个字节64位宽,而virtual address中每个索引值都是9位,因此每个table都是512x8= 4K字节。
虚拟地址对应的意义 (四级表)
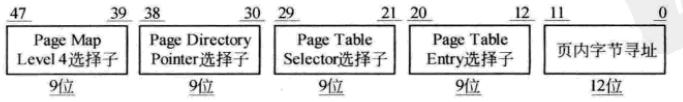
0x376b30
对应二进制: 000000000 000000001(9位) 1 0111 0110(9位) 1011 0011 0000(12位)
对应选择子(索引) 0 1 176 b30
Windbg调试:
PROCESS 88713b58 SessionId: 1 Cid: 0724 Peb: 7ffde000 ParentCid: 056c
DirBase: 7f33c3c0 ObjectTable: 9a1d3cb8 HandleCount: 7.
Image: Helloworld.exe
kd> ! dq 7f33c3c0
#7f33c3c0 00000000`36c1f801 00000000`36e20801
#7f33c3d0 00000000`370a1801 00000000`38122801
#7f33c3e0 00000000`0e343801 00000000`0e444801
#7f33c3f0 00000000`0dd45801 00000000`0e4c6801
#7f33c400 00000000`395ce801 00000000`3964f801
#7f33c410 00000000`7a350801 00000000`38d51801
#7f33c420 00000000`0e654801 00000000`0df55801
#7f33c430 00000000`0e356801 00000000`0e2d7801
kd> ! dq 36c1f000
#36c1f000 00000000`3823e867 00000000`375bd867
#36c1f010 00000000`3794a867 00000000`00000000
#36c1f020 00000000`00000000 00000000`00000000
#36c1f030 00000000`00000000 00000000`00000000
#36c1f040 00000000`00000000 00000000`00000000
#36c1f050 00000000`00000000 00000000`00000000
#36c1f060 00000000`00000000 00000000`00000000
#36c1f070 00000000`00000000 00000000`00000000
kd> ! dq 375bd000+176*8
#375bdbb0 80000000`3e73a025 80000000`383ff025
#375bdbc0 80000000`382d0025 80000000`39078867
#375bdbd0 80000000`38e6f025 80000000`37b51025
#375bdbe0 80000000`3a53b025 80000000`3d4d4025
#375bdbf0 80000000`37602025 00000000`00000000
#375bdc00 00000000`00000000 00000000`00000000
#375bdc10 00000000`00000000 00000000`00000000
#375bdc20 00000000`00000000 00000000`00000000
kd> ! db 3e73a000+b30
#3e73ab30 48 65 6c 6c 6f 57 6f 72-6c 64 00 00 25 70 0d 0a HelloWorld..%p..
#3e73ab40 00 00 00 00 00 6c 37 00-10 6d 37 00 68 6e 37 00 .....l7..m7.hn7.
#3e73ab50 8c 6e 37 00 cc 6e 37 00-00 6f 37 00 01 00 00 00 .n7..n7..o7.....
#3e73ab60 00 00 00 00 01 00 00 00-01 00 00 00 01 00 00 00 ................
#3e73ab70 01 00 00 00 53 74 61 63-6b 20 61 72 6f 75 6e 64 ....Stack around
#3e73ab80 20 74 68 65 20 76 61 72-69 61 62 6c 65 20 27 00 the variable '.
#3e73ab90 27 20 77 61 73 20 63 6f-72 72 75 70 74 65 64 2e ' was corrupted.
#3e73aba0 00 00 00 00 54 68 65 20-76 61 72 69 61 62 6c 65 ....The variable
找到HelloWorld