确切的说这是fwaas,即防火墙即是服务。
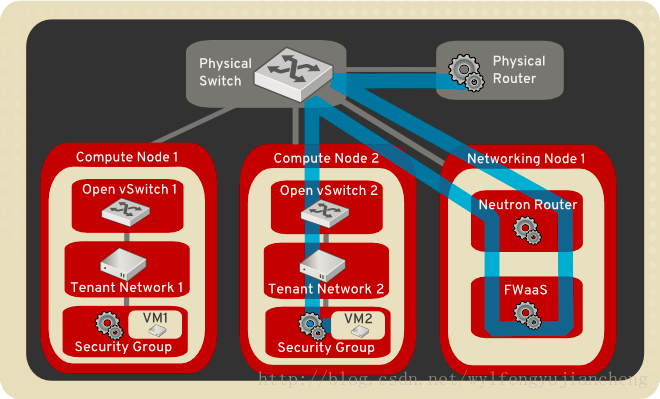
防火墙与安全组区别
防火墙一般放在网关上,用来隔离子网之间的访问。因此,防火墙即服务也是在网络节点上(具体说来是在路由器命名空间中)来实现。
安全组的对象是虚拟网卡,由L2 Agent来实现,比如neutron_openvswitch_agent 和 neutron_linuxbridge_agent,会在计算节点上通过配置 iptables 规则来限制虚拟网卡的进出访问。防火墙可以在安全组之前隔离外部过来的恶意流量,但是对于同个子网内部不同虚拟网卡间的通讯不能过滤(除非它要跨子网)。
部署防火墙
我部署的是mitaka版本
在控制节点和网络节点:
yum install openstack-neutron-fwaas python-neutron-fwaas
控制节点:
修改配置文件 /etc/neutron/neutron.conf
service_plugins = router,neutron.services.firewall.fwaas_plugin.FirewallPlugin
配置数据库
neutron-db-manage --config-file /etc/neutron/neutron.conf --config-file /etc/neutron/plugin.ini --service fwaas upgrade
配置dashboard
vim /usr/share/openstack-dashboard/openstack_dashboard/local/local_settings.py 'enable_firewall' = True
网络节点:
修改配置文件/etc/neutron/fwaas_driver.ini
[DEFAULT] [fwaas] driver = neutron.services.firewall.drivers.linux.iptables_fwaas.IptablesFwaasDriver enabled = True [service_providers] service_provider= FIREWALL:Iptables:neutron.agent.linux.iptables_firewall.OVSHybridIptablesFirewallDriver:default
# 修改系统脚本
修改系统脚本 [root@network system]# vim neutron-l3-agent.service [root@network system]# cat neutron-l3-agent.service [Unit] Description=OpenStack Neutron Layer 3 Agent After=syslog.target network.target [Service] Type=simple User=neutron ExecStart=/usr/bin/neutron-l3-agent --config-file /usr/share/neutron/neutron-dist.conf --config-dir /usr/share/neutron/l3_agent --config-file /etc/neutron/neutron.conf --config-dir /etc/neutron/conf.d/common --config-dir /etc/neutron/conf.d/neutron-l3-agent --config-file /etc/neutron/fwaas_driver.ini --log-file /var/log/neutron/l3-agent.log PrivateTmp=false KillMode=process [Install] WantedBy=multi-user.target [root@network system]# pwd /usr/lib/systemd/system 然后 [root@network system]# systemctl daemon-reload [root@network system]# systemctl restart neutron-l3-agent
然后重启服务
systemctl restart neutron-server #控制节点 systemctl restart httpd.service memcached.service #控制节点 systemctl restart neutron-l3-agent.service # 网络节点
防火墙的使用示例
创建防火墙规则
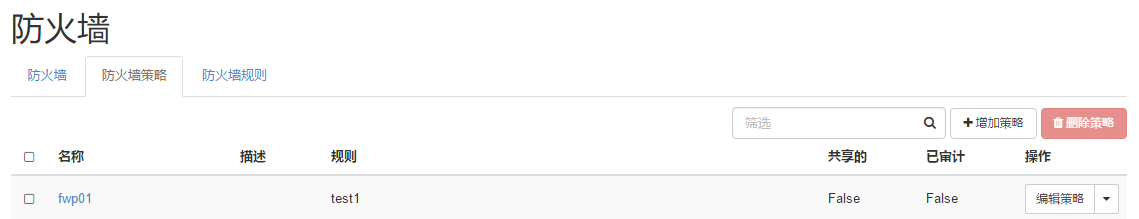
创建防火墙策略
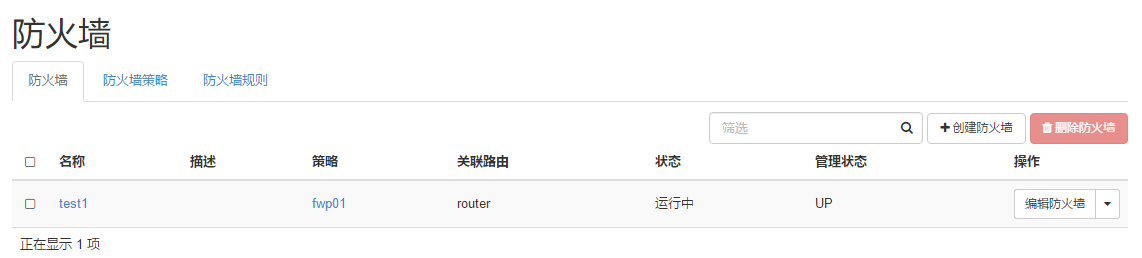
创建防火墙并应用的router路由器
防火墙分析流程
我事先在防火墙上下了2个规则,’icmp source 10.0.0.0/24 drop ‘, ‘tcp source 2.2.2.0/24 des 3.3.3.0/24 drop’,并应用到路由器。
INPUT
iptables –line-numbers -vnL INPUT
ip netns exec qrouter-6d975099-f0d9-49a8-bae8-8bf936c95e1c iptables --line-numbers -vnL INPUT Chain INPUT (policy ACCEPT 489 packets, 19560 bytes) num pkts bytes target prot opt in out source destination 1 749 29960 neutron-l3-agent-INPUT all -- * * 0.0.0.0/0 0.0.0.0/0
iptables –line-numbers -vnL neutron-l3-agent-INPUT
ip netns exec qrouter-6d975099-f0d9-49a8-bae8-8bf936c95e1c iptables --line-numbers -vnL neutron-l3-agent-INPUT Chain neutron-l3-agent-INPUT (1 references) num pkts bytes target prot opt in out source destination 1 0 0 ACCEPT all -- * * 0.0.0.0/0 0.0.0.0/0 mark match 0x1/0xffff 2 0 0 DROP tcp -- * * 0.0.0.0/0 0.0.0.0/0 tcp dpt:9697
可见在INPUT接受所有的数据包
OUTPUT
iptables –line-numbers -vnL OUTPUT
ip netns exec qrouter-6d975099-f0d9-49a8-bae8-8bf936c95e1c iptables --line-numbers -vnL OUTPUT Chain OUTPUT (policy ACCEPT 3 packets, 120 bytes) num pkts bytes target prot opt in out source destination 1 14 560 neutron-filter-top all -- * * 0.0.0.0/0 0.0.0.0/0 2 14 560 neutron-l3-agent-OUTPUT all -- * * 0.0.0.0/0 0.0.0.0/0 ip netns exec qrouter-6d975099-f0d9-49a8-bae8-8bf936c95e1c iptables --line-numbers -vnL neutron-filter-top Chain neutron-filter-top (2 references) num pkts bytes target prot opt in out source destination 1 14 560 neutron-l3-agent-local all -- * * 0.0.0.0/0 0.0.0.0/0 ip netns exec qrouter-6d975099-f0d9-49a8-bae8-8bf936c95e1c iptables --line-numbers -vnL neutron-l3-agent-local Chain neutron-l3-agent-local (1 references) num pkts bytes target prot opt in out source destination ip netns exec qrouter-6d975099-f0d9-49a8-bae8-8bf936c95e1c iptables --line-numbers -vnL neutron-l3-agent-OUTPUT Chain neutron-l3-agent-OUTPUT (1 references) num pkts bytes target prot opt in out source destination
可见在OUTPUT链没有什么规则
FORWARD
ip netns exec qrouter-6d975099-f0d9-49a8-bae8-8bf936c95e1c iptables --line-numbers -vnL FORWARD Chain FORWARD (policy ACCEPT 0 packets, 0 bytes) num pkts bytes target prot opt in out source destination 1 0 0 neutron-filter-top all -- * * 0.0.0.0/0 0.0.0.0/0 2 0 0 neutron-l3-agent-FORWARD all -- * * 0.0.0.0/0 0.0.0.0/0 ip netns exec qrouter-6d975099-f0d9-49a8-bae8-8bf936c95e1c iptables --line-numbers -vnL neutron-filter-top Chain neutron-filter-top (2 references) num pkts bytes target prot opt in out source destination 1 14 560 neutron-l3-agent-local all -- * * 0.0.0.0/0 0.0.0.0/0 ip netns exec qrouter-6d975099-f0d9-49a8-bae8-8bf936c95e1c iptables --line-numbers -vnL neutron-l3-agent-local Chain neutron-l3-agent-local (1 references) num pkts bytes target prot opt in out source destination ip netns exec qrouter-6d975099-f0d9-49a8-bae8-8bf936c95e1c iptables --line-numbers -vnL neutron-l3-agent-FORWARD Chain neutron-l3-agent-FORWARD (1 references) num pkts bytes target prot opt in out source destination 1 0 0 neutron-l3-agent-scope all -- * * 0.0.0.0/0 0.0.0.0/0 2 0 0 neutron-l3-agent-iv45e26bf33 all -- * qr-+ 0.0.0.0/0 0.0.0.0/0 3 0 0 neutron-l3-agent-ov45e26bf33 all -- qr-+ * 0.0.0.0/0 0.0.0.0/0 4 0 0 neutron-l3-agent-fwaas-defau all -- * qr-+ 0.0.0.0/0 0.0.0.0/0 5 0 0 neutron-l3-agent-fwaas-defau all -- qr-+ * 0.0.0.0/0 0.0.0.0/0
neutron-l3-agent-FORWARD很重要,在没有防火墙应用到路由之前,只有条目1,应用防火墙之后,生成了2,3,4,5 我们分别看一下它们具体的内容。
ip netns exec qrouter-6d975099-f0d9-49a8-bae8-8bf936c95e1c iptables --line-numbers -vnL neutron-l3-agent-iv45e26bf33 Chain neutron-l3-agent-iv45e26bf33 (1 references) num pkts bytes target prot opt in out source destination 1 0 0 DROP all -- * * 0.0.0.0/0 0.0.0.0/0 state INVALID 2 0 0 ACCEPT all -- * * 0.0.0.0/0 0.0.0.0/0 state RELATED,ESTABLISHED 3 0 0 DROP tcp -- * * 2.2.2.0/24 3.3.3.0/24 tcp spt:30 dpt:30 4 0 0 DROP icmp -- * * 10.0.0.0/24 0.0.0.0/0 ip netns exec qrouter-6d975099-f0d9-49a8-bae8-8bf936c95e1c iptables --line-numbers -vnL neutron-l3-agent-ov45e26bf33 Chain neutron-l3-agent-ov45e26bf33 (1 references) num pkts bytes target prot opt in out source destination 1 0 0 DROP all -- * * 0.0.0.0/0 0.0.0.0/0 state INVALID 2 0 0 ACCEPT all -- * * 0.0.0.0/0 0.0.0.0/0 state RELATED,ESTABLISHED 3 0 0 DROP tcp -- * * 2.2.2.0/24 3.3.3.0/24 tcp spt:30 dpt:30 4 0 0 DROP icmp -- * * 10.0.0.0/24 0.0.0.0/0 ip netns exec qrouter-6d975099-f0d9-49a8-bae8-8bf936c95e1c iptables --line-numbers -vnL neutron-l3-agent-fwaas-defau Chain neutron-l3-agent-fwaas-defau (2 references) num pkts bytes target prot opt in out source destination 1 0 0 DROP all -- * * 0.0.0.0/0 0.0.0.0/0
这正是我在前面提到的规则,我们发现一条规则下发后分别存在进出两条规则在router中,即neutron-l3-agent-iv45e26bf33 ,neutron-l3-agent-ov45e26bf33 ,用于进数据网络的包的默认处理和出数据网络的包的默认处理。 neutron-l3-agent-fwaas-defau用于默认丢弃没有被以上规则处理的所有包。
我们在此基础上又添加一条规则’‘udp source 7.7.0.0/16 des 8.8.8.0/24 REJECT’’,默认新加的规则在前两者之前,当然我们可以控制这条规则的位置,加入我们把它放在前面两个规则之间,查看如下:
ip netns exec qrouter-6d975099-f0d9-49a8-bae8-8bf936c95e1c iptables --line-numbers -vnL neutron-l3-agent-ov45e26bf33 Chain neutron-l3-agent-ov45e26bf33 (1 references) num pkts bytes target prot opt in out source destination 1 0 0 DROP all -- * * 0.0.0.0/0 0.0.0.0/0 state INVALID 2 0 0 ACCEPT all -- * * 0.0.0.0/0 0.0.0.0/0 state RELATED,ESTABLISHED 3 0 0 DROP tcp -- * * 2.2.2.0/24 3.3.3.0/24 tcp spt:30 dpt:30 4 0 0 REJECT udp -- * * 7.7.0.0/16 8.8.8.0/24 udp spt:89 dpt:900 reject-with icmp-port-unreachable 5 0 0 DROP icmp -- * * 10.0.0.0/24 0.0.0.0/0 ip netns exec qrouter-6d975099-f0d9-49a8-bae8-8bf936c95e1c iptables --line-numbers -vnL neutron-l3-agent-iv45e26bf33 Chain neutron-l3-agent-iv45e26bf33 (1 references) num pkts bytes target prot opt in out source destination 1 0 0 DROP all -- * * 0.0.0.0/0 0.0.0.0/0 state INVALID 2 0 0 ACCEPT all -- * * 0.0.0.0/0 0.0.0.0/0 state RELATED,ESTABLISHED 3 0 0 DROP tcp -- * * 2.2.2.0/24 3.3.3.0/24 tcp spt:30 dpt:30 4 0 0 REJECT udp -- * * 7.7.0.0/16 8.8.8.0/24 udp spt:89 dpt:900 reject-with icmp-port-unreachable 5 0 0 DROP icmp -- * * 10.0.0.0/24 0.0.0.0/0
防火墙有一定顺序,一条一条匹配的,所以规则的顺序也是值得关注的。