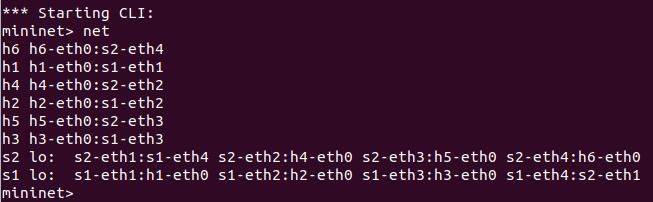
1. 利用mininet创建如下拓扑,要求拓扑支持OpenFlow 1.3协议,主机名、交换机名以及端口对应正确,请给出拓扑Mininet执行结果,展示端口连接情况
1.1创建拓扑

1.2展示网络信息
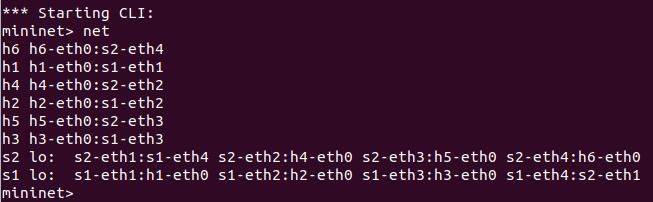
1.3端口连接情况
2. 直接在Open vSwitch下发流表,用vlan得到下列虚拟网段,请逐条说明所下发的流表含义
- 将主机1,2,3进入s1的包打上vlan tag,转发端口4
sudo ovs-ofctl -O OpenFlow13 add-flow s1 priority=1,in_port=1,actions=push_vlan:0x8100,set_field:4096->vlan_vid,output:4
sudo ovs-ofctl -O OpenFlow13 add-flow s1 priority=1,in_port=2,actions=push_vlan:0x8100,set_field:4097->vlan_vid,output:4
sudo ovs-ofctl -O OpenFlow13 add-flow s1 priority=1,in_port=3,actions=push_vlan:0x8100,set_field:4098->vlan_vid,output:4
- 将从端口4的包去除vlan tag, 并根据tag进行转发
sudo ovs-ofctl -O OpenFlow13 add-flow s1 priority=1,dl_vlan=0,actions=pop_vlan,output:1
sudo ovs-ofctl -O OpenFlow13 add-flow s1 priority=1,dl_vlan=1,actions=pop_vlan,output:2
sudo ovs-ofctl -O OpenFlow13 add-flow s1 priority=1,dl_vlan=2,actions=pop_vlan,output:3
- 将主机4,5,6进入s2的包打上vlan tag,转发端口4
sudo ovs-ofctl -O OpenFlow13 add-flow s2 priority=1,in_port=1,actions=push_vlan:0x8100,set_field:4096->vlan_vid,output:4
sudo ovs-ofctl -O OpenFlow13 add-flow s2 priority=1,in_port=2,actions=push_vlan:0x8100,set_field:4097->vlan_vid,output:4
sudo ovs-ofctl -O OpenFlow13 add-flow s2 priority=1,in_port=3,actions=push_vlan:0x8100,set_field:4098->vlan_vid,output:4
- 将从端口4的包去除vlan tag, 并根据tag进行转发
sudo ovs-ofctl -O OpenFlow13 add-flow s2 priority=1,dl_vlan=0,actions=pop_vlan,output:1
sudo ovs-ofctl -O OpenFlow13 add-flow s2 priority=1,dl_vlan=1,actions=pop_vlan,output:2
sudo ovs-ofctl -O OpenFlow13 add-flow s2 priority=1,dl_vlan=2,actions=pop_vlan,output:3
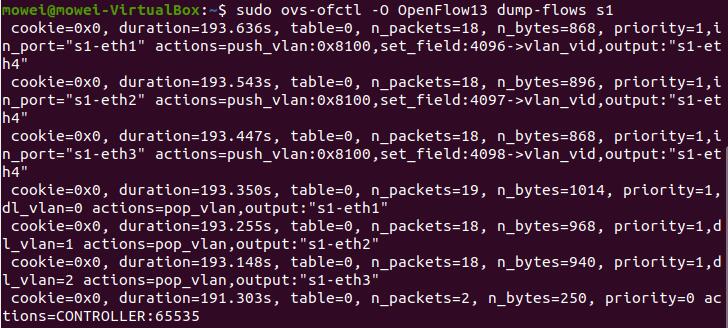
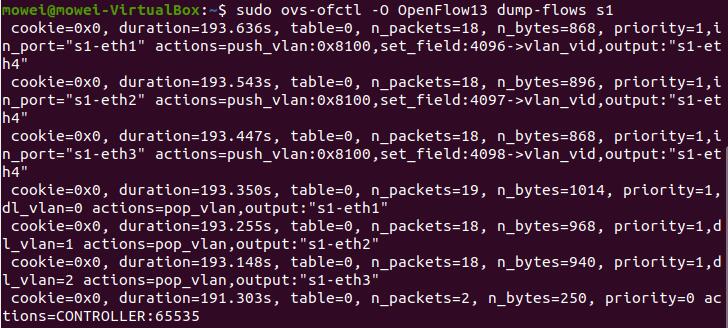
3. 直接在Open vSwitch查看流表,提交OVS命令执行结果
sudo ovs-ofctl -O OpenFlow13 dump-flows s1
sudo ovs-ofctl -O OpenFlow13 dump-flows s2

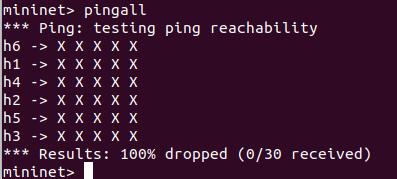
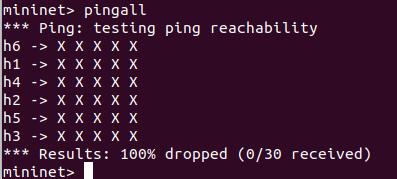
4. 提交主机连通性测试结果,验证流表的有效性

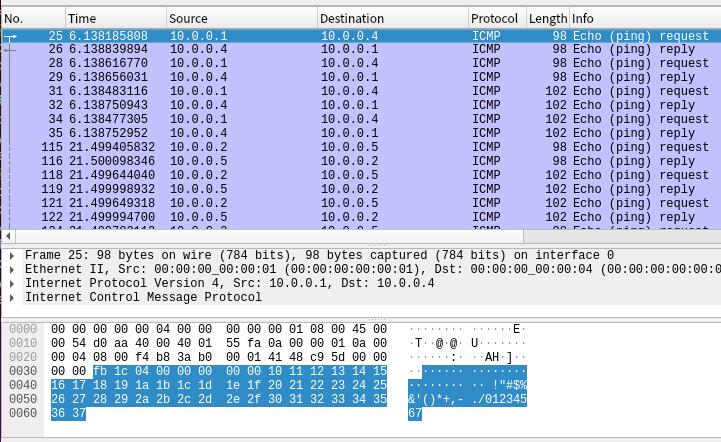
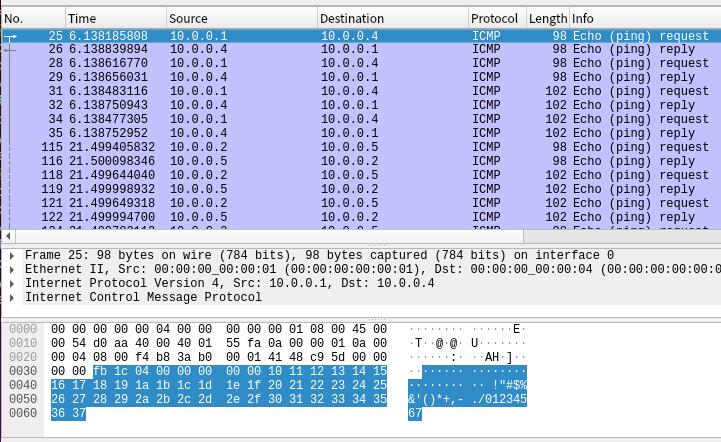
5. 利用Wireshark抓包,分析验证特定报文